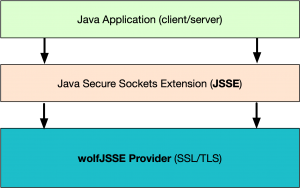
The Java Secure Socket Extension (JSSE) framework supports the installation of security providers. These providers can implement a subset of the functionality used by the Java JSSE security APIs, including SSL/TLS. We are happy to announce the availability of the wolfJSSE Provider, which wraps the native wolfSSL SSL/TLS library. With this provider, users can leverage all the advantages of native wolfSSL from Java applications! These advantages include TLS 1.3 support, performance optimizations, hardware cryptography support, FIPS 140-2 validation, and much more!
The wolfSSL JSSE provider (wolfJSSE) is distributed along with the wolfSSL JNI wrapper. Version 1.5.0 is now available from the wolfSSL download page (wolfssl-jni-jsse-1.5.0.zip). wolfJSSE has currently been tested on several JDK’s, including Oracle JDK, OpenJDK, Android OSP, and Zulu JDK. If you would like to use wolfJSSE on a different JDK or platform, let us know at facts@wolfssl.com!
There are several example applications that ship as part of the JSSE download, including an example Client and Server, which make it easier to get up and running quickly. The provider can be installed at runtime per application, or at the system level for all Java Security API consumers to use.
Initial benchmarking between native wolfSSL, wolfJSSE, and the default SunJSSE provider client on Mac are below:
| Client and Configuration | Avg. Connection Time |
|---|---|
| wolfSSL C only (no Java, software) | 9.694 ms |
| wolfSSL C only (no Java, intelasm + sp + sp-asm) | 7.302 ms |
| wolfJSSE Client (software only) | 10.92 ms |
| wolfJSSE Client (sp + intelasm) | 8.42 ms |
| wolfJSSE Client (TLS 1.3 sp + intelasm) | 8.04 ms |
| SunJSSE Provider client (default on Mac) | 13.34 ms |
NOTE: TLS 1.2 cipher suite used in above benchmarks: ECDHE-RSA-AES256-GCM-SHA384
To learn more, please see the following documentation pages:
wolfSSL JSSE Provider (and JNI wrapper) Product Page
wolfSSL Java JSSE Provider User Manual
Installing a JSSE Provider in Android OSP
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.

