RECENT BLOG NEWS
How to use TLS with JAVA
When developing an application that needs to communicate securely with another device TLS is a great option. The framework in place for TLS connections with JAVA is JSSE (Java Secure Socket Extension). JSSE is a set of interfaces that can be called to abstract the TLS process and make it easy for plugging in different security providers while keeping an application unchanged after initial integration. wolfJSSE is an open source implementation of these interfaces that uses the embedded IoT wolfSSL library for it’s cryptography operations. There are many ways to interact with JSSE when adding in security, two of the common ways are with creating a SSL socket or by creating a SSL engine. A simple example of creating and using SSL sockets for both the client and server side can be found in the “examples/provider” directory on the wolfssljni repository located here (https://github.com/wolfSSL/wolfssljni). In addition to interacting with JSSE directly there are packages in JAVA that use it. One such package deals with URL connections and can be used for creating HTTPS connections. An example of a simple HTTPS connection using it can be found in the “java” directory of the wolfSSL examples repository (https://github.com/wolfSSL/wolfssl-examples).
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
Improved NXP MMCAU Crypto Hardware Performance
The NXP Memory-Mapped Cryptographic Acceleration Unit (mmCAU) is on many Kinetis microcontrollers. It improves symmetric AES and SHA performance as compared to our software based implementation. wolfSSL version 4.2.0 enhanced mmCAU support to use multiple blocks against hardware and optimize to avoid memory copies (memcpy) when possible. This resulted in a 20-78% improvement in performance!
Features:
- Enhancement for NXP mmCAU to process more than one block at a time.
- Added optional buffer alignment detection macro, WC_HASH_DATA_ALIGNMENT, to avoid memcpy.
- Added MD5 and SHA-1 support for XTRANSFORM_LEN to process blocks.
- Cleanups for consistency between algorithms and code commenting.
Improved MMCAU performance: SHA-1 by 35%, SHA-256 by 20% and MD5 by 78%.
NXP K64 MMCAU with wolfSSL v4.2.0: MD5 8 MB took 1.000 seconds, 7.910 MB/s SHA 4 MB took 1.005 seconds, 3.644 MB/s SHA-256 2 MB took 1.006 seconds, 2.306 MB/s NXP K64 MMCAU with wolfSSL v4.1.0: MD5 4 MB took 1.004 seconds, 4.450 MB/s SHA 3 MB took 1.006 seconds, 2.670 MB/s SHA-256 2 MB took 1.008 seconds, 1.913 MB/s
Changes are in GitHub pull request #2481 and in the wolfSSL v4.3.0 release.
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
We love you,
wolfSSL Team
CMS/PKCS #7 RSA Sign Callback for Raw Digest Signature Generation
We have added many new features in our new release of wolfSSL 4.3.0. One new feature we have added is a CMS/PKCS #7 callback for signing SignedData raw digests – enabled with the macro HAVE_PKCS7_RSA_RAW_SIGN_CALLBACK and call to function wc_PKCS7_SetRsaSignRawDigestCb().
For those who are unaware PKCS #7 is used to sign and/or encrypt messages under a PKI. Used also for certificate dissemination (for instance as a response to a PKCS #10 message), it formed the basis for S/MIME, which is as of 2010 based on RFC 5652, an updated Cryptographic Message Syntax Standard (CMS). Often used for single sign-on.
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
We love you.
Team wolfSSL
Updates to RSA-PSS salt lengths
In our new release of wolfSSL 4.3.0 we have added updates to RSA-PSS salt lengths. The macro WOLFSSL_PSS_SALT_LEN_DISCOVER value into wc_RsaPSS_Verify_ex() attempts to discover salt length and can use larger salt lengths.
RSA-PSS is a probabilistic signature scheme (PSS) with appendix. A signature scheme with appendix requires the message itself to verify the signature (i.e. the message is not recoverable from the signature). RSA-PSS is an adaptation of their work and is standardized as part of PKCS#1 v2.1. In general, RSA-PSS should be used as a replacement for RSA-PKCS#1 v1.5.
RSA-PSS parameters
- hash algorithm/function. The default is SHA-1.
- mask generation function (MGF). Currently always MGF1.
- salt length. The default value is 20 but the convention is to use hLen, the length of the output of the hash function in bytes. A salt length of zero is permitted and will result in a deterministic signature value. The actual salt length used can be determined from the signature value.
- trailer field, used in the encoding operation. The default trailer field is the byte 0xbc. There are no options to change this value.
The default parameters for RSA-PSS are:
hashAlgorithm sha1, maskGenAlgorithm mgf1SHA1 (the function MGF1 with SHA-1) saltLength 20, trailerField trailerFieldBC (the byte 0xbc)
It is recommended that the MGF hash function be the same as the scheme hash algorithm/function, and that the salt length be hLen, the length of the output of the hash function.
For more information on RSA-PSS visit https://www.cryptosys.net/pki/manpki/pki_rsaschemes.html
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
We love you.
Team wolfSSL
Check out our Webinar on TLS 1.3, OpenSSL COMPARISON!
wolfSSL: TLS 1.3, OpenSSL comparison
wolfSSL’s open-source SSL/TLS library is constantly updated to maintain a mature code base and adapts quickly to any standard changes. One recent change is the release of TLS 1.3 (successor of TLS 1.2 which was out for 10 years).
What is new in TLS 1.3?
TLS 1.3 brought forth numerous improvements including faster handshake times, full session encryption and new cipher suites. There are faster handshake times as there is only one RTT instead of two which enables clients to send data immediately after the first reply from the server. Full session encryption is also achieved through the use of a variety of encryption algorithms to secure data. In addition, new cipher suites considered to be stronger also come with TLS 1.3.
How are we different from OpenSSL?
There are several key differentiators between wolfSSL and OpenSSL. These include the following:
- Build size (up to 20x smaller than OpenSSL)
- Standards support: up to date on most recent standards
- Hardware acceleration
- Team of security experts
- Ease of Use designed for developers
- Portability: a long list of supported platforms
- Dual license: GPLv2 or Commercial
- 24/7 Support
To watch all the wolfSSL webinars, check out our YouTube channel:
https://www.youtube.com/channel/UCxcGPWzOnhdocvKmxqhfvPg?view_as=subscriber
To read more about the differences between TLS 1.2 and TLS 1.3 visit:
https://www.wolfssl.com/differences-between-tls-12-and-tls-13-12/
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
wolfMQTT Client Supports Secure AWS
The wolfMQTT client library has an Amazon Web Services example that demonstrates securely connecting over TLS provided by the wolfSSL embedded SSL/TLS library.
We setup an AWS IoT endpoint and testing device certificate. The AWS server uses a TLS client certificate for authentication. The example is located in `/examples/aws/`. It subscribes to `$aws/things/”AWSIOT_DEVICE_ID”/shadow/update/delta` and publishes to `$aws/things/”AWSIOT_DEVICE_ID”/shadow/update`.
Everyone deserves to have their IoT data secure, and wolfSSL provides the best libraries to accomplish that! wolfSSL supports up to TLS 1.3, FIPS 140-2, expansive support for hardware cryptography, and more! Secure-IoT-Love from the wolfSSL team!
You can download the latest release here: https://www.wolfssl.com/download/
Or clone directly from our GitHub repository.
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
wolfSSL Conforms to MISRA-C:2012 Guidelines
The team at wolfSSL has taken the core functionality of the wolfSSL embedded SSL/TLS library to the next level and implemented changes to conform to the Required and Mandatory rules from the MISRA-C:2012 Guidelines.
Currently a subset of the wolfCrypt files are checked (sha256.c, aes.c (CBC/GCM), rsa.c, random.c, sp_c64.c), let us know if your project requires other files and we can target them while expanding coverage.
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
wolfSSL Java JSSE Provider Now Available
The Java Secure Socket Extension (JSSE) framework supports the installation of security providers. These providers can implement a subset of the functionality used by the Java JSSE security APIs, including SSL/TLS. We are happy to announce the availability of the wolfJSSE Provider, which wraps the native wolfSSL SSL/TLS library. With this provider, users can leverage all the advantages of native wolfSSL from Java applications! These advantages include TLS 1.3 support, performance optimizations, hardware cryptography support, FIPS 140-2 validation, and much more!
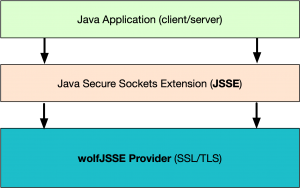
The wolfSSL JSSE provider (wolfJSSE) is distributed along with the wolfSSL JNI wrapper. Version 1.5.0 is now available from the wolfSSL download page (wolfssl-jni-jsse-1.5.0.zip). wolfJSSE has currently been tested on several JDK’s, including Oracle JDK, OpenJDK, Android OSP, and Zulu JDK. If you would like to use wolfJSSE on a different JDK or platform, let us know at facts@wolfssl.com!
There are several example applications that ship as part of the JSSE download, including an example Client and Server, which make it easier to get up and running quickly. The provider can be installed at runtime per application, or at the system level for all Java Security API consumers to use.
Initial benchmarking between native wolfSSL, wolfJSSE, and the default SunJSSE provider client on Mac are below:
| Client and Configuration | Avg. Connection Time |
|---|---|
| wolfSSL C only (no Java, software) | 9.694 ms |
| wolfSSL C only (no Java, intelasm + sp + sp-asm) | 7.302 ms |
| wolfJSSE Client (software only) | 10.92 ms |
| wolfJSSE Client (sp + intelasm) | 8.42 ms |
| wolfJSSE Client (TLS 1.3 sp + intelasm) | 8.04 ms |
| SunJSSE Provider client (default on Mac) | 13.34 ms |
NOTE: TLS 1.2 cipher suite used in above benchmarks: ECDHE-RSA-AES256-GCM-SHA384
To learn more, please see the following documentation pages:
wolfSSL JSSE Provider (and JNI wrapper) Product Page
wolfSSL Java JSSE Provider User Manual
Installing a JSSE Provider in Android OSP
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
Support for STM32_PKA Accelerator
wolfSSL is a proud partner of STMicroelectronics, and we support a great many of their products. Now we have added support for the STM32_PKA accelerator found in the STM32WB55 module.
The STM32WB55 module is is a heterogeneous dual-core MCU with a Cortex-M4 for the end-user application and a Cortex-M0 for the BLE stack. This PKA module accelerates ECC sign and verification. The measured performance is 160ms per ECC SECP256R1 verification. This option is enabled with the WOLFSSL_STM32_PKA build option and is demonstrated with our wolfBoot library.
Support added in PR 2498:
https://github.com/wolfSSL/wolfssl/pull/2498
wolfBoot implementation details can be found here.
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
We love you.
Team wolfSSL
wolfSSL Support for DO-178 DAL A
wolfSSL now provides support for complete RTCA DO-178C level A certification! wolfSSL will offer DO-178 wolfCrypt as a commercial off -the-shelf (COTS) solution for connected avionics applications. Adherence to DO-178C level A will be supported through the first wolfCrypt COTS DO-178C certification kit release that includes traceable artifacts for the following encryption algorithms:
- SHA-256 for message digest
- AES for encryption and decryption
- RSA to sign and verify a message.
- Chacha20_poly1305 for authenticated encryption and decryption.
The primary goal of this initial release is to provide the proper cryptographic underpinnings for secure boot and secure firmware update in commercial and military avionics. wolfSSL brings trusted, military-grade security to connected commercial and military aircraft. Avionics developers now have a flexible, compact, economical, high-performance COTS solution for quickly delivering FIPS 140-2 validated crypto algorithms can be used in DO-178 mode for combined FIPS 140-2/DO-178 consumption. The wolfCrypt cryptography library FIPS 140-2 validation certificates can be applied to DO-178 uses.
Optimization Support
We understand that securely rebooting avionic systems has rigorous performance requirements. As such, we’re here to help with cryptographic performance optimizations through our services organization.
To download and view the most recent version of wolfSSL, the wolfSSL GitHub repository can be cloned from here: https://github.com/wolfssl/wolfssl.git, and the most recent stable release can be downloaded from the wolfSSL download page here: https://www.wolfssl.com/download/.
wolfSSL DO-178 product page: https://www.wolfssl.com/wolfssl-support-178-dal/.
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
Weekly updates
Archives
- April 2025 (21)
- March 2025 (22)
- February 2025 (21)
- January 2025 (23)
- December 2024 (22)
- November 2024 (29)
- October 2024 (18)
- September 2024 (21)
- August 2024 (24)
- July 2024 (27)
- June 2024 (22)
- May 2024 (28)
- April 2024 (29)
- March 2024 (21)
- February 2024 (18)
- January 2024 (21)
- December 2023 (20)
- November 2023 (20)
- October 2023 (23)
- September 2023 (17)
- August 2023 (25)
- July 2023 (39)
- June 2023 (13)
- May 2023 (11)
- April 2023 (6)
- March 2023 (23)
- February 2023 (7)
- January 2023 (7)
- December 2022 (15)
- November 2022 (11)
- October 2022 (8)
- September 2022 (7)
- August 2022 (12)
- July 2022 (7)
- June 2022 (14)
- May 2022 (10)
- April 2022 (11)
- March 2022 (12)
- February 2022 (22)
- January 2022 (12)
- December 2021 (13)
- November 2021 (27)
- October 2021 (11)
- September 2021 (14)
- August 2021 (10)
- July 2021 (16)
- June 2021 (13)
- May 2021 (9)
- April 2021 (13)
- March 2021 (24)
- February 2021 (22)
- January 2021 (18)
- December 2020 (19)
- November 2020 (11)
- October 2020 (3)
- September 2020 (20)
- August 2020 (11)
- July 2020 (7)
- June 2020 (14)
- May 2020 (13)
- April 2020 (14)
- March 2020 (4)
- February 2020 (21)
- January 2020 (18)
- December 2019 (7)
- November 2019 (16)
- October 2019 (14)
- September 2019 (18)
- August 2019 (16)
- July 2019 (8)
- June 2019 (9)
- May 2019 (28)
- April 2019 (27)
- March 2019 (15)
- February 2019 (10)
- January 2019 (16)
- December 2018 (24)
- November 2018 (9)
- October 2018 (15)
- September 2018 (15)
- August 2018 (5)
- July 2018 (15)
- June 2018 (29)
- May 2018 (12)
- April 2018 (6)
- March 2018 (18)
- February 2018 (6)
- January 2018 (11)
- December 2017 (5)
- November 2017 (12)
- October 2017 (5)
- September 2017 (7)
- August 2017 (6)
- July 2017 (11)
- June 2017 (7)
- May 2017 (9)
- April 2017 (5)
- March 2017 (6)
- January 2017 (8)
- December 2016 (2)
- November 2016 (1)
- October 2016 (15)
- September 2016 (6)
- August 2016 (5)
- July 2016 (4)
- June 2016 (9)
- May 2016 (4)
- April 2016 (4)
- March 2016 (4)
- February 2016 (9)
- January 2016 (6)
- December 2015 (4)
- November 2015 (6)
- October 2015 (5)
- September 2015 (5)
- August 2015 (8)
- July 2015 (7)
- June 2015 (9)
- May 2015 (1)
- April 2015 (4)
- March 2015 (12)
- January 2015 (4)
- December 2014 (6)
- November 2014 (3)
- October 2014 (1)
- September 2014 (11)
- August 2014 (5)
- July 2014 (9)
- June 2014 (10)
- May 2014 (5)
- April 2014 (9)
- February 2014 (3)
- January 2014 (5)
- December 2013 (7)
- November 2013 (4)
- October 2013 (7)
- September 2013 (3)
- August 2013 (9)
- July 2013 (7)
- June 2013 (4)
- May 2013 (7)
- April 2013 (4)
- March 2013 (2)
- February 2013 (3)
- January 2013 (8)
- December 2012 (12)
- November 2012 (5)
- October 2012 (7)
- September 2012 (3)
- August 2012 (6)
- July 2012 (4)
- June 2012 (3)
- May 2012 (4)
- April 2012 (6)
- March 2012 (2)
- February 2012 (5)
- January 2012 (7)
- December 2011 (5)
- November 2011 (7)
- October 2011 (5)
- September 2011 (6)
- August 2011 (5)
- July 2011 (2)
- June 2011 (7)
- May 2011 (11)
- April 2011 (4)
- March 2011 (12)
- February 2011 (7)
- January 2011 (11)
- December 2010 (17)
- November 2010 (12)
- October 2010 (11)
- September 2010 (9)
- August 2010 (20)
- July 2010 (12)
- June 2010 (7)
- May 2010 (1)
- January 2010 (2)
- November 2009 (2)
- October 2009 (1)
- September 2009 (1)
- May 2009 (1)
- February 2009 (1)
- January 2009 (1)
- December 2008 (1)

