RECENT BLOG NEWS
TLS 1.3 combined with FIPS (#FIPS #TLS13)
wolfSSL is a lightweight TLS/SSL library that is targeted for embedded devices and systems. It has support for the TLS 1.3 protocol, which is a secure protocol for transporting data between devices and across the Internet. In addition, wolfSSL uses the wolfCrypt encryption library to handle its data encryption.
Because there is a FIPS 140-2 validated version of wolfCrypt, this means that wolfSSL not only has support for the most current version of TLS, but it also has the encryption backbone to support your FIPS 140-2 needs if required.
Some key benefits of combining TLS 1.3 with FIPS validated software include:
- Software becomes marketable to federal agencies - without FIPS, a federal agency is not able to use cryptographic-based software
- Single round trip
- 0-RTT (a mode that enable zero round trip time)
- After Server Hello, all handshake messages are encrypted.
And much more! For more information regarding the benefits of using TLS 1.3 or using the FIPS validated version of wolfCrypt, check out wolfSSL's TLS 1.3 Protocol Support and our wolfCrypt FIPS page.
FIPS 140-2 is a government validation that certifies that an encryption module has successfully passed rigorous testing and meets high encryption standards as specified by NIST. For more information or details on FIPS 140-2, it may be helpful to view this Wikipedia article: https://en.wikipedia.org/wiki/FIPS_140-2
For more details about wolfSSL, TLS 1.3, or if you have any other general inquiries please contact facts@wolfssl.com
To find out more about FIPS, check out the NIST FIPS publications or contact fips@wolfssl.com
wolfSSL at TRON Symposium (TRONSHOW) 2018
wolfSSL will be exhibiting at the 2018 TRON Symposium (TRONSHOW). wolfSSL will be exhibiting from 10:00am to 5:00pm, on December 12th-14th.
The TRON Symposium 2018 will be located at the Tokyo Midtown Hall, with wolfSSL exhibiting at booth B2.
Tokyo Midtown Hall: Akasaka 9-7-1, Minato-ku, Tokyo (directions)
Stop by to hear about the wolfSSL embedded SSL/TLS library which provides support for the latest versions of TLS, wolfTPM, wolfMQTT, wolfSSH, or any of the other wolfSSL products which provide the link between TLS and hardware security. We look forward to seeing you there!
For questions, feel free to contact facts@wolfssl.com.
wolfBoot – wolfSSL’s Secure Bootloader
wolfSSL is pleased to announce the first ever release of wolfBoot!
wolfBoot v1.0 release page: https://github.com/wolfSSL/wolfBoot/releases/tag/v1.0
wolfBoot is a secure bootloader that leverages wolfSSL's underlying wolfCrypt module to provide signature authentication for the running firmware.
The role of a secure bootloader is to effectively prevent the loading of malicious or unauthorized firmware on the target. Additionally, wolfBoot provides a fail-safe update mechanism, that can be interrupted at any time, and resumed at next boot.
wolfBoot is designed to be a portable, OS-agnostic, secure bootloader solution for all 32-bit microcontrollers, relying on wolfCrypt for firmware authentication.
Due to its minimalist design and the tiny Hardware Abstraction Layer (HAL) API, wolfBoot is completely independent of any OS or bare-metal application, and can be easily ported and integrated into existing embedded software solutions.
wolfBoot provides the basis for secure firmware update (OTA) management at boot time, cutting down the development effort needed to implement and validate the required mechanisms to handle the updates. It reduces the development effort to just receiving the image using a secure channel within the application/OS. We recommend using wolfSSL to encrypt the firmware transfer over TLS, to avoid eavesdropping. Once the image is transferred and stored into the update partition, wolfBoot takes care of the update procedure at the next boot.
Remote updates that would lead to a faulty firmware are automatically reverted by wolfBoot after the first 'test' boot, by restoring the original firmware image whenever the update has failed to boot properly. This mechanism protects the target device from accidental updates on the field.
wolfBoot can be downloaded from the wolfSSL download page here: https://www.wolfssl.com/download/
More about boot loaders can be found here: https://en.wikipedia.org/wiki/Booting#BOOT-LOADER
More about wolfSSL: https://www.wolfssl.com/products/wolfssl/
More about wolfCrypt: https://www.wolfssl.com/products/wolfCrypt/
Contact facts@wolfssl.com for any questions or for more information
wolfSSL support for Asio and Boost.Asio C++ Libraries
Recently, wolfSSL released version 3.15.5. This new release contains many new feature additions and updates, including the addition of several new ports. One of these ports is for replacing OpenSSL with wolfSSL in the Asio and Boost.Asio C++ libraries!
Asio is a cross-platform C++ library for network and low-level I/O programming that provides developers with a consistent asynchronous model using a modern C++ approach. It is used in a multitude of different projects and is included as part of the core C++ Boost libraries as Boost.Asio.
As of right now, our changes to the Asio repository are still in the process of being merged upstream. However, If you are interested in using Asio with wolfSSL in your project don’t hesitate to contact us at facts@wolfssl.com and we will send you the required source code. Then, follow the instruction in the rest of this blog post to learn how to build Asio with wolfSSL.
After cloning or downloading the latest version of wolfSSL from GitHub, execute the following commands from the wolfSSL root directory.
$ ./autogen.sh $ ./configure --enable-asio $ make $ sudo make install
After cloning or downloading the latest version of Asio from GitHub, execute the following commands from the Asio root directory. Asio can be downloaded from GitHub here: https://github.com/chriskohlhoff/asio
$ ./autogen.sh $ ./configure --with-wolfssl=/path/to/wolfSSL/installation #(i.e. /usr/local) $ make $ sudo make install
To run Asio’s unit tests and ensure everything has been built correctly with wolfSSL, you can run the following command:
$ make check
The wolfSSL compatible Asio version relies on the preprocessor statement “ASIO_USE_WOLFSSL” to function correctly. You may need to define this when compiling your application or you can insert “#include <wolfssl/options.h>” before any SSL related Asio header files are declared.
For more information on building and installing Asio, view the Asio documentation.
Until wolfSSL support for Asio has been merged into the stable releases of Boost, you will have to manually replace Boost.Asio in the current Boost release with the wolfSSL compatible version. To do this, follow the instructions below.
In the root directory of the wolfSSL compatible Asio download, execute the following command to convert the standalone Asio version into the Boost.Asio version.
$ ./boostify.pl
You will now need to copy the asio directory located in asio/boostified/libs/asio/include/boost and replace the asio directory in your Boost download. The asio directory in Boost can be found in boost_1_67_0/boost
You can now build and install Boost to your system by running the following command from the Boost root directory.
$ ./bootstrap.sh $ ./b2 $ sudo ./b2 install
The preprocessor statement that Boost.Asio relies on is “BOOST_ASIO_USE_WOLFSSL”.
That's it! You should now be able to run your own applications that use Asio or Boost.Asio with wolfSSL!
For more information or help with getting Asio and wolfSSL into your project, please contact us at facts@wolfssl.com.
Expanded PKCS#7 support
Recently, wolfSSL released version 3.15.5. This new release of wolfSSL features many new updates, one of which is expanded support for PKCS#7 Cryptographic Message Syntax (CMS). This contains support for using PKCS#7 with Key-Encryption Key Recipient Info (KEKRI), Password Recipient Info (PWRI), and Other Recipient Info (ORI) types.
PKCS#7 is used to sign, encrypt, or decrypt messages under Public Key Infrastructure (PKI). It is also used for certificate dissemination, but is most commonly used for single sign-on.
This expanded PKCS#7 support improves how implementations using wolfSSL handle receiving various RecipientInfo types that were not supported, and also allows wolfSSL to more accurately determine the information and details about each recipient.
Additionally, wolfSSL also provides support for TLS 1.3, which includes many new features such as handshake speedups, removal of insecure algorithms, and improved encryption requirements.
For more information, feel free to contact support@wolfssl.com.
Resources
wolfSSL 3.15.5 release notes: https://www.wolfssl.com/wolfssl-3-15-5-now-available/
PKCS Wikipedia article: https://en.wikipedia.org/wiki/PKCS
TLS 1.3: https://www.wolfssl.com/docs/tls13/
wolfSSL Yocto Project and OpenEmbedded Support
 Did you know that wolfSSL, wolfSSH, wolfMQTT, and wolfTPM all support being compiled on Yocto Project or OpenEmbedded based projects? We recently refreshed our layer and recipe files to support the most current product versions, examples, and Open Source project bbappend files.
Did you know that wolfSSL, wolfSSH, wolfMQTT, and wolfTPM all support being compiled on Yocto Project or OpenEmbedded based projects? We recently refreshed our layer and recipe files to support the most current product versions, examples, and Open Source project bbappend files.
There are a several ways that projects can include wolfSSL products, or the wolfSSL embedded SSL/TLS library in Yocto Project / OE images. wolfSSL maintains a layer called “meta-wolfssl“, located on GitHub here:
https://github.com/wolfssl/meta-wolfssl
This layer includes recipes for:
- wolfSSL embedded SSL/TLS library
- wolfSSH lightweight SSH library
- wolfMQTT lightweight MQTT Client Library
- wolfTPM TPM 2.0 Library
- wolfCrypt test application
- wolfCrypt benchmark application
- cURL .bbappend file, for compiling cURL with wolfSSL support
If you are interested in trying these recipes out, we have a great Getting Started document available here:
wolfSSL Getting Started for Yocto and OpenEmbedded
The wolfSSL product recipe is also part of the “meta-openembedded/meta-networking/recipes-connectivity” layer, located here:
If you have questions about using “meta-wolfssl” in your project, or need tips on getting started with your build, email us at facts@wolfssl.com!
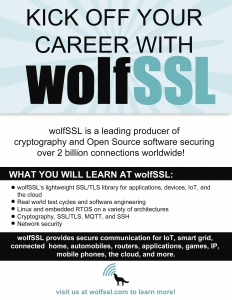
wolfSSL Summer of Security Internship Program
Are you a student looking to gain experience in Internet Security, including SSL/TLS, cryptography, MQTT, SSH, and TPM 2.0? wolfSSL is one of the leading producers of Open Source Internet security products, securing over 2 Billion active connections on the Internet today. The wolfSSL “Summer of Security” program is a Summer internship in Bozeman, MT and Edmonds, WA which spans the Summer months and brings qualified students on-board to learn about how security software is written, tested, and used around the world.
The Summer of Security program allows wolfSSL interns to gain knowledge in the embedded SSL/TLS industry as well as valuable programming experience in Linux and embedded systems. Throughout the Summer, interns will play a role in improving documentation, current examples, test cases, and community support within wolfSSL and related products.
The Summer of Security is a great opportunity for students to increase work experience in the field of Computer Science and work towards a potential career as part of the wolfSSL team. The team at wolfSSL looks for knowledgeable students who have experience in C programming. Prior embedded systems experience, network programming experience, and familiarity with git/GitHub are a plus.
Apply Today!
If you are interested in learning more about the wolfSSL Summer of Security internship program, please send a resume and cover letter to us at facts@wolfssl.com!
Learn More
wolfSSL Homepage
wolfSSL Products Page
wolfSSL User Manual
TLS 1.3 Support!
wolfSSL Examples Repository (GitHub)
wolfSSL now supports latest Intel QuickAssist v1.7 driver and hardware
wolfSSL now has added support for:
- Intel QuickAssist driver v1.7 (qat1.7.l.4.3.0-00033)
- Intel QuickAssist 8970 hardware
- QuickAssist accelerated RSA Key Gen
- QuickAssist accelerated SHA 3
The new 8970 hardware has 12 additional cryptographic hardware instances. The previous 8950 cards had 6 instances and the new ones have 18. The 8970 card also adds a PCIe (Gen 3) 16x option for increased performance.
For example, using the Intel QuickAssist 8970 (PCIe 16x) hardware on an i7-2600 CPU @ 3.40GHz with 8 threads running, we achieved the following asymmetric benchmarks:
- RSA 2048 public 289,559 ops/sec
- RSA 2048 private 41,929 ops/sec
- DH 2048 key gen 65,534 ops/sec
- DH 2048 agree 89,587 ops/sec
- ECDHE 256 agree 55,745 ops/sec
- ECDSA 256 sign 59,674 ops/sec
- ECDSA 256 verify 32,804 ops/sec
More wolfSSL benchmark data can be found on the wolfSSL benchmarks page, here: https://www.wolfssl.com/docs/benchmarks/
Intel QuickAssist: https://www.intel.com/content/www/us/en/architecture-and-technology/intel-quick-assist-technology-overview.html
If you are interested in evaluating the wolfSSL Asynchronous support for Intel QuickAssist or Cavium Nitrox, please email us at facts@wolfssl.com.
wolfSSL Micrium uC/OS-III and uC/TCP-IP Support
Are you a user of Micrium? If so, you will be happy to know that wolfSSL recently updated support and added TLS client and server examples to the wolfSSL embedded SSL/TLS library for Micrium!
We have also run a benchmark of our wolfCrypt/wolfSSL libraries on an NXP Kinetis K70 (Freescale TWR-K70F120M MCU) tower system board with a project built using the IAR Embedded Workbench IDE - ARM 8.32.1 (IAR ELF Linker V8.32.1.169/W32 for ARM). The details can be viewed on the wolfSSL benchmarks page.
For instructions on how to build and integrate the examples on your projects or to see the benchmark results, please see the README located in “IDE/ECLIPSE/MICRIUM”. This support is currently located in our GitHub master branch, and will roll into the next stable release of wolfSSL as well. For any questions or help getting wolfSSL up and running on your environment, please contact us at support@wolfssl.com. wolfSSL also now supports the most current version of TLS, TLS 1.3! Learn more here: https://www.wolfssl.com/docs/tls13/ !
wolfSSL smallstack size reduction
wolfSSL v3.15.5 was released last week which features many new additions to the library. One of those new additions is the reduction of the stack usage while using the “smallstack” build option.
The goal of wolfSSL’s “smallstack” build is to use at most 1kB of stack. All other memory used is placed on the heap.
Currently, wolfSSL passes the option "--enable-smallstack" to the configure script. The small stack option can also be enabled by defining the following option: WOLFSSL_SMALL_STACK
Please contact support@wolfssl.com with any questions about building the wolfSSL embedded SSL/TLS library for your platform, or customizing the memory usage of wolfSSL.
Weekly updates
Archives
- April 2025 (19)
- March 2025 (22)
- February 2025 (21)
- January 2025 (23)
- December 2024 (22)
- November 2024 (29)
- October 2024 (18)
- September 2024 (21)
- August 2024 (24)
- July 2024 (27)
- June 2024 (22)
- May 2024 (28)
- April 2024 (29)
- March 2024 (21)
- February 2024 (18)
- January 2024 (21)
- December 2023 (20)
- November 2023 (20)
- October 2023 (23)
- September 2023 (17)
- August 2023 (25)
- July 2023 (39)
- June 2023 (13)
- May 2023 (11)
- April 2023 (6)
- March 2023 (23)
- February 2023 (7)
- January 2023 (7)
- December 2022 (15)
- November 2022 (11)
- October 2022 (8)
- September 2022 (7)
- August 2022 (12)
- July 2022 (7)
- June 2022 (14)
- May 2022 (10)
- April 2022 (11)
- March 2022 (12)
- February 2022 (22)
- January 2022 (12)
- December 2021 (13)
- November 2021 (27)
- October 2021 (11)
- September 2021 (14)
- August 2021 (10)
- July 2021 (16)
- June 2021 (13)
- May 2021 (9)
- April 2021 (13)
- March 2021 (24)
- February 2021 (22)
- January 2021 (18)
- December 2020 (19)
- November 2020 (11)
- October 2020 (3)
- September 2020 (20)
- August 2020 (11)
- July 2020 (7)
- June 2020 (14)
- May 2020 (13)
- April 2020 (14)
- March 2020 (4)
- February 2020 (21)
- January 2020 (18)
- December 2019 (7)
- November 2019 (16)
- October 2019 (14)
- September 2019 (18)
- August 2019 (16)
- July 2019 (8)
- June 2019 (9)
- May 2019 (28)
- April 2019 (27)
- March 2019 (15)
- February 2019 (10)
- January 2019 (16)
- December 2018 (24)
- November 2018 (9)
- October 2018 (15)
- September 2018 (15)
- August 2018 (5)
- July 2018 (15)
- June 2018 (29)
- May 2018 (12)
- April 2018 (6)
- March 2018 (18)
- February 2018 (6)
- January 2018 (11)
- December 2017 (5)
- November 2017 (12)
- October 2017 (5)
- September 2017 (7)
- August 2017 (6)
- July 2017 (11)
- June 2017 (7)
- May 2017 (9)
- April 2017 (5)
- March 2017 (6)
- January 2017 (8)
- December 2016 (2)
- November 2016 (1)
- October 2016 (15)
- September 2016 (6)
- August 2016 (5)
- July 2016 (4)
- June 2016 (9)
- May 2016 (4)
- April 2016 (4)
- March 2016 (4)
- February 2016 (9)
- January 2016 (6)
- December 2015 (4)
- November 2015 (6)
- October 2015 (5)
- September 2015 (5)
- August 2015 (8)
- July 2015 (7)
- June 2015 (9)
- May 2015 (1)
- April 2015 (4)
- March 2015 (12)
- January 2015 (4)
- December 2014 (6)
- November 2014 (3)
- October 2014 (1)
- September 2014 (11)
- August 2014 (5)
- July 2014 (9)
- June 2014 (10)
- May 2014 (5)
- April 2014 (9)
- February 2014 (3)
- January 2014 (5)
- December 2013 (7)
- November 2013 (4)
- October 2013 (7)
- September 2013 (3)
- August 2013 (9)
- July 2013 (7)
- June 2013 (4)
- May 2013 (7)
- April 2013 (4)
- March 2013 (2)
- February 2013 (3)
- January 2013 (8)
- December 2012 (12)
- November 2012 (5)
- October 2012 (7)
- September 2012 (3)
- August 2012 (6)
- July 2012 (4)
- June 2012 (3)
- May 2012 (4)
- April 2012 (6)
- March 2012 (2)
- February 2012 (5)
- January 2012 (7)
- December 2011 (5)
- November 2011 (7)
- October 2011 (5)
- September 2011 (6)
- August 2011 (5)
- July 2011 (2)
- June 2011 (7)
- May 2011 (11)
- April 2011 (4)
- March 2011 (12)
- February 2011 (7)
- January 2011 (11)
- December 2010 (17)
- November 2010 (12)
- October 2010 (11)
- September 2010 (9)
- August 2010 (20)
- July 2010 (12)
- June 2010 (7)
- May 2010 (1)
- January 2010 (2)
- November 2009 (2)
- October 2009 (1)
- September 2009 (1)
- May 2009 (1)
- February 2009 (1)
- January 2009 (1)
- December 2008 (1)