RECENT BLOG NEWS
Job Posting: Embedded Systems Software Engineer
wolfSSL is a growing company looking to add a top notch embedded systems software engineer to our organization. wolfSSL develops, markets and sells the leading Open Source embedded SSL/TLS protocol implementation, wolfSSL. Our users are primarily building devices or applications that need security. Other products include wolfCrypt embedded cryptography engine, wolfMQTT client library, and wolfSSH.
Job Description:
Currently, we are seeking to add a senior level C software engineer with 5-10 years experience interested in a fun company with tremendous upside. Backgrounds that are useful to our team include networking, security, and hardware optimizations. Assembly experience is a plus. Experience with encryption software is a plus. RTOS experience is a plus. Experience with hardware-based cryptography is a plus.
Operating environments of particular interest to us include Linux, Windows, Embedded Linux and RTOS varieties (VxWorks, QNX, ThreadX, uC/OS, MQX, FreeRTOS, etc). Experience with mobile environments such as Android and iOS is also a plus, but not required.
Location is flexible. For the right candidate, we’re open to this individual working from virtually any location.
How To Apply
To apply or discuss, please send your resume and cover letter to facts@wolfssl.com.
wolfSSL and ST at Embedded World 2018
wolfSSL recently exhibited at Embedded World in Germany, where we did a quick video interview with ST. The video highlights the STM32 platform support we have in the wolfSSL embedded TLS library and the demo that we were showing off during the exhibition. wolfSSL engineer David Garske talks about wolfSSL’s hardware crypto support on the STM32F7 as demonstrated by a wolfCrypt benchmark demo. Watch our interview on YouTube, here:
The demo mentioned in the video is available on GitHub, here.
If you are interested in securing your STM32-based IoT, RTOS, or embedded project with wolfSSL, contact us at facts@wolfssl.com for some tips! wolfSSL also supports TLS 1.3!
New wolfSSL Blog Subscription Feature
The wolfSSL blog now has a new feature that allows individuals to subscribe to weekly updates. Users can add their email to the subscription list, and upon verifying their emails, they will receive a weekly update on Mondays at 9am MDT of the latest updates to the wolfSSL blog. This allows users to keep up to speed on the wolfSSL embedded TLS library, TLS 1.3, FIPS, hardware crypto, performance optimization, and more!
To view this feature and try it out for yourself, visit the wolfSSL blog today!
wolfSSL FAQ page
The wolfSSL FAQ page can be useful for information or general questions that need need answers immediately. It covers some of the most common questions that the support team receives, along with the support team's responses. It's a great resource for questions about wolfSSL, embedded TLS, and for solutions to problems getting started with wolfSSL.
To view this page for yourself, please follow this link here.
Here is a sample list of 5 questions that the FAQ page covers:
- How do I build wolfSSL on ... (*NIX, Windows, Embedded device) ?
- How do I manage the build configuration of wolfSSL?
- How much Flash/RAM does wolfSSL use?
- How do I extract a public key from a X.509 certificate?
- Is it possible to use no dynamic memory with wolfSSL and/or wolfCrypt?
Have a question that isn't on the FAQ? Feel free to email us at support@wolfssl.com.
Unit Test Additions in wolfSSL 3.14.0
wolfSSL is committed to leveraging Continuous Integration in the design, delivery, and evaluation of our software – where development and testing are an ongoing process. As such, wolfSSL continues to make improvements to the quality of its testing throughout the software life-cycle to meet the needs of embedded IoT devices. Release 3.14.0 adds expanded unit testing for the following algorithms:
- Ed25519,
- Elliptic Curve Cryptography (ECC),
- AES CMAC,
- SHA 3, and
- RSA-PSS.
The addition of roughly fifty unit test functions increases our test coverage in the wolfSSL embedded TLS library. Unit testing along with the wolfCrypt testing functions provide both white and black box testing methodology in an effort to increase the security of the software. wolfSSL strives to be the most thoroughly tested SSL/TLS library available. Our testing process is intended to rigorously examine the execution paths of our software as well as test the correctness of the algorithms implemented.
For a more comprehensive view into our testing process, feel free to read our previous blog post on the different types of testing we do at wolfSSL! And, as always, please contact us at facts@wolfssl.com with any questions.
Updated PKCS#7 Support in wolfSSL 3.14.0
wolfSSL recently expanded our PKCS#7 support in the wolfSSL embedded TLS library with the addition of:
- Functional parsing of multiple certificates in SignedData types
- Support for parsing SignedData degenerate types
- A getter function for retrieving bundle attributes
- Internal BER to DER translation
- A public API for PKCS#7 type padding
Expanding on the feature list above, our PKCS#7 certificate handling prior to wolfSSL 3.14.0 parsed only the first certificate in the chain when a SignedData bundle contained multiple certificates. As of 3.14.0, wolfSSL is now able to parse multiple certificates.
The pad function, wc_PKCS7_PadData(), adds pad bytes to the input data and operates on a particular block size.
In wolfSSL 3.14.0, we added a translation function for internally converting from BER ASN.1 encoding to DER encoding for interoperability, as well as adding a getter function (wc_PKCS7_GetAttributeValue()) to return data attribute values.
Lastly, support for PKCS#7 degenerate SignedData types, where there are no signers on the content was added. The degenerate case provides means for disseminating certificates and certificate-revocation lists, as defined in RFC 2315. These additions to wolfSSL’s PKCS#7 support further strengthen the security for IoT devices requiring TLS functionality.
wolfSSL and Static Memory on FreeRTOS
We are proud to announce that wolfSSL’s static memory feature with FreeRTOS received an update in our latest 3.14.0 release. This feature allows for memory allocation to stack memory instead of using the heap. In previous versions of the wolfSSL embedded TLS library, the library would not compile when trying to use FreeRTOS and static memory. With this update, when FREERTOS is defined, the static memory feature uses pvPortMalloc() instead of malloc() when WOLFSSL_NO_MALLOC is not defined and a heap hint is not used.
With this new behavior when handling memory allocation in an RTOS environment wolfSSL now supports using only stack where supported.
For more information about building wolfSSL on embedded, IoT, and/or RTOS environments with static memory enabled please visit our static buffer allocation documentation page.
wolfSSL Performance on Intel x86_64 (Part 6)
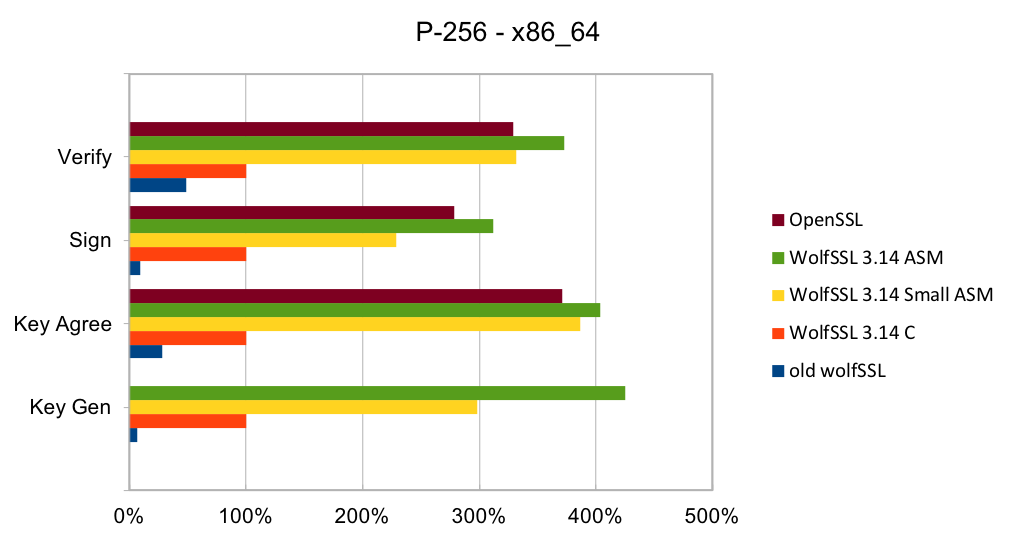
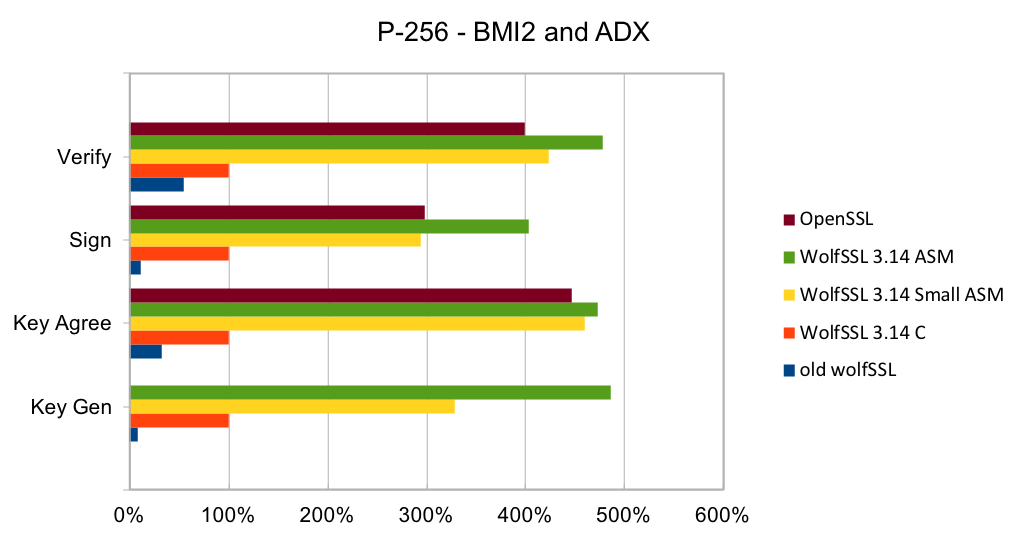
Recent releases of wolfSSL have included new assembly code targeted at the Intel x86_64 platform. Large performance gains have been made and are being discussed over six blog posts of which this is the last part. In this blog, we will talk about the performance of Elliptic Curve (EC) operations over the P-256 curve.
Elliptic curve cryptography (ECC) is the alternative to finite field (FF) cryptography which has algorithms like RSA, DSA and DH. ECDSA is the elliptic curve variant of RSA and DSA while ECDH is the elliptic curve variant of DH. ECDSA and ECDH can be used anywhere their FF counterparts can be used. ECC requires a pre-defined curve to perform the operations on. The most commonly used curve is P-256 as it has 128-bit strength and is in many standards including TLS, for certificates in IETF, and NIST’s FIPS 186-4. Browsers and web servers are preferring ECDH over DH as it is much faster.
wolfSSL 3.13 and later have completely new implementations of the EC algorithms over the P-256 curve. The implementation is constant-time with respect to private key operations. The implementations include variants in C, and assembly code targeted at Intel x86_64 and x86_64 with BMI2 and ADX. There is a small code size variant of the assembly code that is about 1/3rd the size (smaller pre-computed tables) yet remains very fast.
The two charts below show the relative performance of the old wolfSSL code, new small wolfSSL assembly code, new fast wolfSSL assembly code and OpenSSL as compared to the new wolfSSL C implementation on Ivy Bridge and Skylake CPUs. Note that the OpenSSL super-app does not measure the speed of the ECDH key generation operation. The new C implementation is a lot faster than the old generic C/ASM code for both CPUs. The assembly code is many times better than the C code mostly due to the use of larger pre-computed tables of elliptic curve points. The OpenSSL code is around 10% slower than the new fast wolfSSL assembly code using the generic x86_64 code and between 5% and 35% slower than wolfSSL assembly code for x86_64 with BMI2 and ADX instructions.
Contact us at support@wolfssl.com with questions about the performance of the wolfSSL embedded TLS library.
References:
ECDSA (Elliptic Curve Digital Signature Algorithm)
ECDH (Elliptic-curve Diffie–Hellman)
wolfSSL Performance on Intel x86_64 (Part 5)
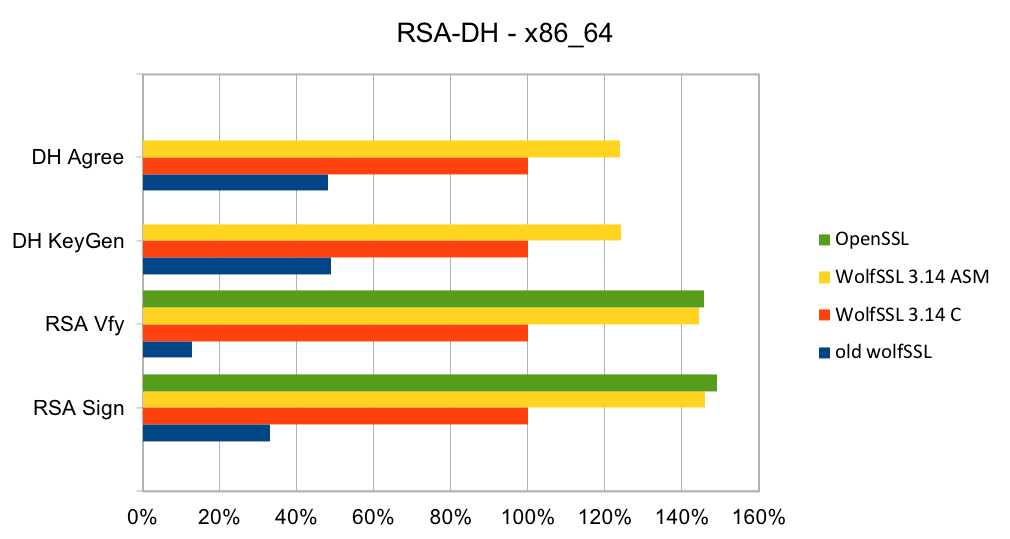
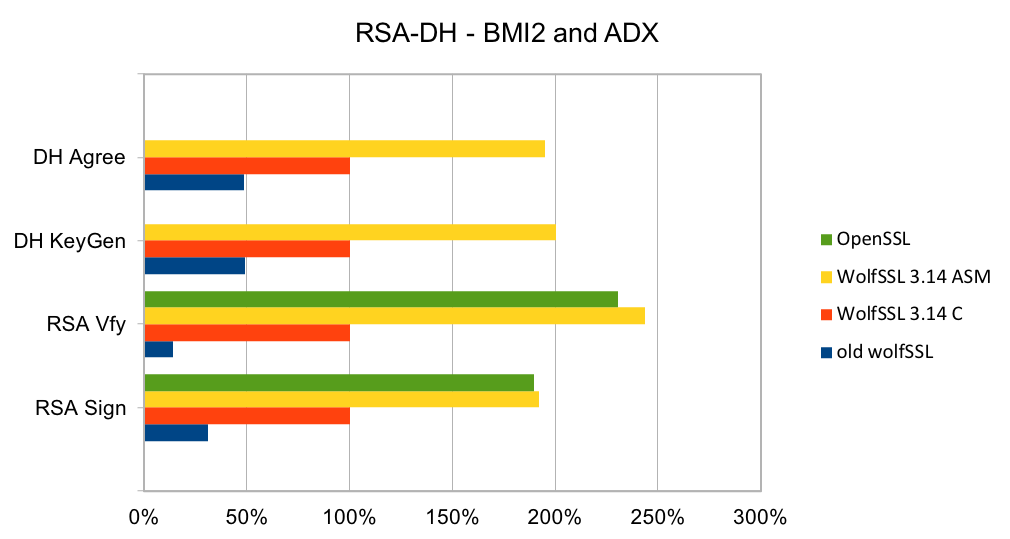
Recent releases of wolfSSL have included new assembly code targeted at the Intel x86_64 platform. Large performance gains have been made and are being discussed over six blog posts of which this is part 5. In this blog, we will talk about the performance of RSA and Diffie-Hellman (DH).
RSA is the most commonly used public key algorithm for certificates. When performing a TLS handshake, the server will sign a hash of the messages seen so far and the client will verify the signature of certificates in the certificate chain and verify the hash of messages with the public key in the certificate. Signing and verifying are the most time-consuming operations in a handshake.
DH has been the key exchange algorithm of choice in handshakes but is falling out of favor as the Elliptic Curve variants are considerably faster at the same security level. Performing the key exchange is the second most time-consuming operation in a TLS handshake.
wolfSSL 3.13 and later have completely new implementations of RSA and DH targeted at specific key sizes: 2048 and 3072 bits. The implementation is constant-time with respect to private key operations. The implementations include variants in C and assembly code targeted at Intel x86_64 and x86_64 with BMI2 and ADX. The new code is significantly better than the old generic code and is about the same speed as OpenSSL on older CPUs and a little faster on newer CPUs.
The two charts below show the relative performance of the old wolfSSL code, new wolfSSL assembly code and OpenSSL as compared to the new wolfSSL C implementation on Ivy Bridge and Skylake CPUs. Note that the OpenSSL super-app does not measure the speed of DH operations. The new C implementation is a lot faster than the old generic C/ASM code for both CPUs. The assembly code for x86_64 is better than the C code by between 23% and 46% on x86_64 and 92% and 144% using BMI2 and ADX instructions. The OpenSSL code is about the same speed as the wolfSSL assembly code.
Contact us at support@wolfssl.com for questions about the performance of the wolfSSL embedded TLS library, using it on your platform, our about our TLS 1.3 support!
References:
wolfSSL Performance on Intel x86_64 (Part 4)
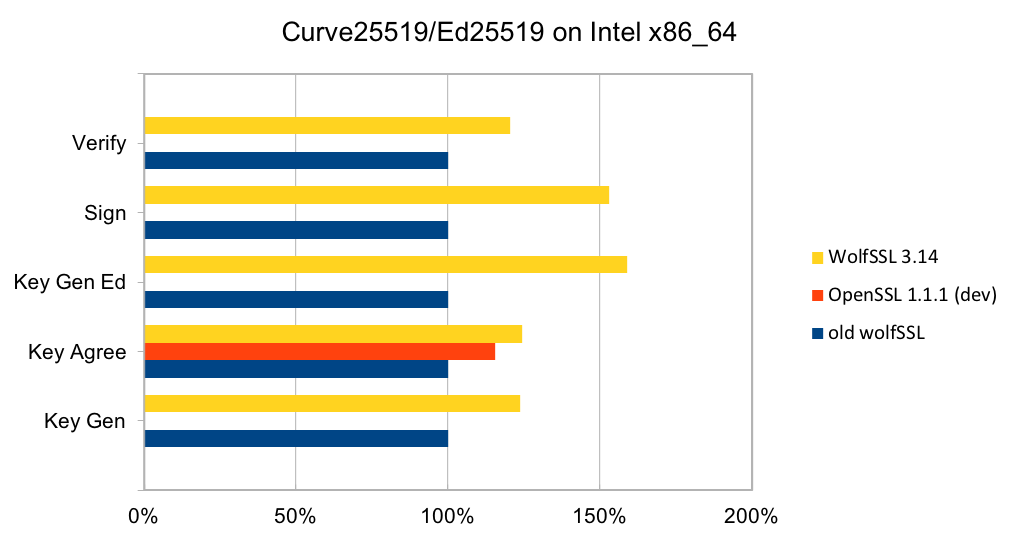
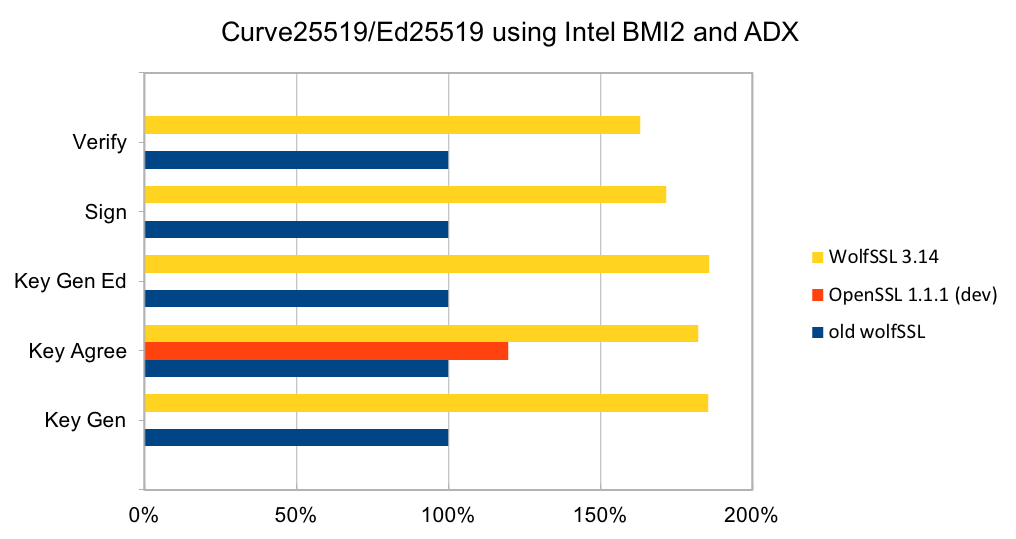
Recent releases of wolfSSL have included new assembly code targeted at the Intel x86_64 platform. Large performance gains have been made and are being discussed over six blog posts of which this is part 4. In this blog, we will talk about the performance of Curve25519 and Ed25519.
Curve25519 is set of parameters for a Montgomery elliptic curve and has ~128-bit security. It is used in key exchange and has become popular due to its speed and inclusion in standards. The algorithm is included as part of TLS v1.3 and NIST is considering it as part of SP 800-186. Ed25519 is set of parameters for a Twisted Edwards curve and is mathematically related to Curve25519 and has the same security properties. A new signature scheme has been designed over Twisted Edwards curves that is fast and included as part of TLS v1.3. A draft specification has been written describing digital certificates using EdDSA with Ed25519.
In a TLS handshake, a key exchange operation should always be performed to ensure forward-secrecy. When used, it will be a significant amount of the processing time during the handshake. Improving the performance of Curve25519, therefore, increases the number of TLS connections that can be made per second.
Older releases of wolfSSL have a C implementation of the algorithms. While the C code was quite fast, the new assembly code is significantly better. There is assembly code for generic Intel x86_64 CPUs, and for CPUs with BMI2 and ADX (Broadwell and newer CPUs).
The two charts below show the relative performance of wolfSSL and OpenSSL compared to the C implementation on Ivy Bridge and Skylake CPUs. On the Ivy Bridge CPU, the new assembly code is between 20% and 60% better than the C code and is better than OpenSSL in the one operation that can be measured. On the Skylake CPU, the assembly code is between 60% and 86% faster. The OpenSSL code has not been optimized for this CPU and is significantly slower.
Contact us at support@wolfssl.com with questions about the performance of the wolfSSL embedded TLS library.
References:
Weekly updates
Archives
- July 2025 (7)
- June 2025 (22)
- May 2025 (25)
- April 2025 (24)
- March 2025 (22)
- February 2025 (21)
- January 2025 (23)
- December 2024 (22)
- November 2024 (29)
- October 2024 (18)
- September 2024 (21)
- August 2024 (24)
- July 2024 (27)
- June 2024 (22)
- May 2024 (28)
- April 2024 (29)
- March 2024 (21)
- February 2024 (18)
- January 2024 (21)
- December 2023 (20)
- November 2023 (20)
- October 2023 (23)
- September 2023 (17)
- August 2023 (25)
- July 2023 (39)
- June 2023 (13)
- May 2023 (11)
- April 2023 (6)
- March 2023 (23)
- February 2023 (7)
- January 2023 (7)
- December 2022 (15)
- November 2022 (11)
- October 2022 (8)
- September 2022 (7)
- August 2022 (12)
- July 2022 (7)
- June 2022 (14)
- May 2022 (10)
- April 2022 (11)
- March 2022 (12)
- February 2022 (22)
- January 2022 (12)
- December 2021 (13)
- November 2021 (27)
- October 2021 (11)
- September 2021 (14)
- August 2021 (10)
- July 2021 (16)
- June 2021 (13)
- May 2021 (9)
- April 2021 (13)
- March 2021 (24)
- February 2021 (22)
- January 2021 (18)
- December 2020 (19)
- November 2020 (11)
- October 2020 (3)
- September 2020 (20)
- August 2020 (11)
- July 2020 (7)
- June 2020 (14)
- May 2020 (13)
- April 2020 (14)
- March 2020 (4)
- February 2020 (21)
- January 2020 (18)
- December 2019 (7)
- November 2019 (16)
- October 2019 (14)
- September 2019 (18)
- August 2019 (16)
- July 2019 (8)
- June 2019 (9)
- May 2019 (28)
- April 2019 (27)
- March 2019 (15)
- February 2019 (10)
- January 2019 (16)
- December 2018 (24)
- November 2018 (9)
- October 2018 (15)
- September 2018 (15)
- August 2018 (5)
- July 2018 (15)
- June 2018 (29)
- May 2018 (12)
- April 2018 (6)
- March 2018 (18)
- February 2018 (6)
- January 2018 (11)
- December 2017 (5)
- November 2017 (12)
- October 2017 (5)
- September 2017 (7)
- August 2017 (6)
- July 2017 (11)
- June 2017 (7)
- May 2017 (9)
- April 2017 (5)
- March 2017 (6)
- January 2017 (8)
- December 2016 (2)
- November 2016 (1)
- October 2016 (15)
- September 2016 (6)
- August 2016 (5)
- July 2016 (4)
- June 2016 (9)
- May 2016 (4)
- April 2016 (4)
- March 2016 (4)
- February 2016 (9)
- January 2016 (6)
- December 2015 (4)
- November 2015 (6)
- October 2015 (5)
- September 2015 (5)
- August 2015 (8)
- July 2015 (7)
- June 2015 (9)
- May 2015 (1)
- April 2015 (4)
- March 2015 (12)
- January 2015 (4)
- December 2014 (6)
- November 2014 (3)
- October 2014 (1)
- September 2014 (11)
- August 2014 (5)
- July 2014 (9)
- June 2014 (10)
- May 2014 (5)
- April 2014 (9)
- February 2014 (3)
- January 2014 (5)
- December 2013 (7)
- November 2013 (4)
- October 2013 (7)
- September 2013 (3)
- August 2013 (9)
- July 2013 (7)
- June 2013 (4)
- May 2013 (7)
- April 2013 (4)
- March 2013 (2)
- February 2013 (3)
- January 2013 (8)
- December 2012 (12)
- November 2012 (5)
- October 2012 (7)
- September 2012 (3)
- August 2012 (6)
- July 2012 (4)
- June 2012 (3)
- May 2012 (4)
- April 2012 (6)
- March 2012 (2)
- February 2012 (5)
- January 2012 (7)
- December 2011 (5)
- November 2011 (7)
- October 2011 (5)
- September 2011 (6)
- August 2011 (5)
- July 2011 (2)
- June 2011 (7)
- May 2011 (11)
- April 2011 (4)
- March 2011 (12)
- February 2011 (7)
- January 2011 (11)
- December 2010 (17)
- November 2010 (12)
- October 2010 (11)
- September 2010 (9)
- August 2010 (20)
- July 2010 (12)
- June 2010 (7)
- May 2010 (1)
- January 2010 (2)
- November 2009 (2)
- October 2009 (1)
- September 2009 (1)
- May 2009 (1)
- February 2009 (1)
- January 2009 (1)
- December 2008 (1)

