RECENT BLOG NEWS
CNSA 2.0 Update Part 3: LMS and XMSS
On April 18th, 2024, the NSA released updates and clarifications to their CNSA 2.0 (Commercial National Security Algorithm Suite 2.0) advisory in the form of an FAQ. This is the third in a multipart series of postings about the questions and answers that we feel are most interesting and our reactions to them.
But first, some clarifications on terms and acronyms:
- NSS: National Security System
- NIST SP 800-208 National Institute of Standard and Technology Special Publication 800-208 titled: Recommendation for Stateful Hash-Based Signature Schemes
- LMS: Leighton-Micali Signatures; a stateful hash-based signature scheme
- HSS: Hierarchical Signature Scheme; the hyper-tree algorithm that is on top of LMS
- XMSS: eXtended Merkle Signature Scheme; a stateful hash-based signature scheme
- XMSS^MT: eXtended Merkle Signature Scheme – Multi-Tree; the hyper-tree algorithm that is on top of XMSS
Q: Can I use HSS or XMSSMT from NIST SP 800-208?
A: From NIST SP 800-208, NSA has only approved LMS and XMSS for use in NSS. The multitree algorithms HSS and XMSSMT are not allowed.
Essentially what this means is that only the actual stateful hash-based signature schemes are approved for usage in NSS. The hyper-tree (colloquially known as “tree of trees”) components specified in NIST SP 800-208 are not approved.
Our implementation supports the hyper-tree components with the actual stateful hash-based signature schemes. More specifically, HSS/LMS and XMSS/XMSS^MT.
It is quite simple to transform an LMS public key into an HSS/LMS public key by putting 4 bytes of zeros in front of the LMS public key. The same is true of the signature.
In addition to the hyper-tree components, we allow for XMSS by supporting the following specifications in our API:
- XMSS-SHA2_10_256
- XMSS-SHA2_16_256
- XMSS-SHA2_20_256
Note the lack of MT.
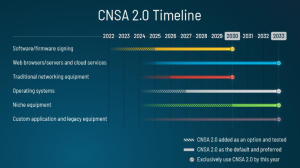
These algorithms are used in our wolfBoot product for firmware verification and are ready for use today and that’s a good thing as the CNSA 2.0 timeline says you need to be ready now.
Here at wolfSSL we are looking forward to the future of post-quantum algorithms. If you need LMS or XMSS that is performant, capable of running in bare metal or resource constrained environments, have a look at our wolfBoot product.
If you have questions about any of the above, please contact us at facts@wolfSSL.com or +1 425 245 8247.
Check out CNSA 2.0 Update Part 1 and Part 2, and stay tuned for more insights in our upcoming blogs!
Download wolfSSL Now
CNSA 2.0 Update Part 2: NIAP
On April 18th, 2024, the NSA released updates and clarifications to their CNSA 2.0 (Commercial National Security Algorithm Suite 2.0) advisory in the form of an FAQ. This is the second in a multipart series of postings about the questions and answers that we feel are most interesting and our reactions to them.
But first, some clarifications on terms and acronyms:
- NIST SP 800-208 National Institute of Standard and Technology Special Publication 800-208 titled: Recommendation for Stateful Hash-Based Signature Schemes
- NIAP: National Information Assurance Partnership: A United States government organization that oversees evaluations of commercial information technology products for use in national security systems
- LMS: Leighton-Micali Signatures; a stateful hash-based signature scheme
- XMSS: eXtended Merkle Signature Scheme; a stateful hash-based signature scheme
- CAVP: The Cryptographic Algorithm Validation Program; provides guidelines for validation testing which is a pre-requisite for CMVP testing
- CMVP: Cryptographic Module Validation Program; security accreditation program for cryptographic modules.
Q: As a commercial vendor, how do I know if my NIST SP 800-208 implementation meets CNSA 2.0?
A: NIAP validates products against its published Protection Profiles, which will start
including quantum-resistant signatures in line with our published transition timelines. For
commercial vendors, we do not anticipate NIAP Protection Profiles will perform
signature generation within the Target of Evaluation (TOE) boundary, only signature
verification. As signature generation is the component of LMS/XMSS that requires state
management, if only signature verification is being performed, only CAVP validation (not
CMVP) will be expected for such products.
Anyone who has been following wolfSSL’s progress with post-quantum algorithms knows we have our own implementations of LMS/HSS and XMSS/XMSS^MT and they are integrated into the wolfBoot product! wolfBoot only uses them to verify the signature of the firmware, therefore one only needs to build these algorithms with verification functionalities. Check out sections 17 and 20 of our wolfSSL INSTALL file.
Requiring only CAVP validation is an excellent bonus for our customers. It means that validation will be a simpler and easier process for our team to help you achieve. You can count on fast turnaround times and little if any paperwork.
Preparing for NIAP and need the best cryptography? Contact us at support@wolfSSL.com or reach out with any questions at facts@wolfSSL.com or +1 425 245 8247.
Catch up on ‘CNSA 2.0 Updated Part 1: Today!‘ and stay tuned for more insights in our upcoming blogs!
Download wolfSSL Now
CNSA 2.0 Update Part 1: Today!
On April 18th, 2024, the NSA released updates and clarifications to their CNSA 2.0 (Commercial National Security Algorithm Suite 2.0) advisory. They did it in the form of an FAQ document (list of Frequently Asked Questions with Answers). The FAQ document was sent to the PQC Forum. This will be a multi-part series of postings about the questions and answers that we feel are most interesting and our reactions to them.
Q: Is there a quantum-resistant public-key algorithm that commercial vendors should adopt today?
A: NSA encourages vendors to use CNSA 2.0 approved hash-based signatures for software- and firmware-signing. NSA does not approve using pre-standardized or non-FIPS-validated CNSA 2.0 algorithms (even in hybrid modes) for NSS missions. However, NSA does recommend limited use of pre-standardized or non-FIPS-validated CNSA 2.0 algorithms and modules in research settings to prepare for the transition. NSA requests vendors begin preparing to implement CNSA 2.0 algorithms so they are primed to provide products soon after NIST completes standardization.
The NSA has spoken and they expect the industries from which they purchase to provide products that support the CNSA 2.0 Algorithm Suite upon standardization. That means DO NOT start when standardization is complete; start now.
Note that for software/firmware signing it says you should already have it added and tested in your system! By next year, it should be the default and preferred. This means if you are not using LMS or XMSS in your boot loader then you are out of compliance with the CNSA 2.0 guidance. Checkout wolfBoot where we have already added support for the stateful hash-based signature schemes.
The NSA is also saying you need to be prepared with these algorithms already integrated into your products. Here at wolfSSL we have been saying the same message for years. You need to prepare for and understand the impacts that the larger keys, cipher text and signatures are going to have on your systems. Will these larger cryptographic artifacts require more memory resources? Will they slow down your transmissions? Will the answer to those questions cascade into new requirements and trade-offs? Now is the time to find the answers to those questions. Contact us at support@wolfSSL.com for benchmarking details.
If you haven’t already, go ahead and get started today. See Appendix G of our wolfSSL manual. Have further questions about getting started with CNSA 2.0 using wolfSSL, contact us at support@wolfSSL.com.
If you have questions about any of the above, please contact us at facts@wolfSSL.com or +1 425 245 8247.
Download wolfSSL Now
Live Webinar: How to Determine FIPS Compliance for Government Buyers
In today’s security-conscious world, ensuring that your technology solutions meet stringent compliance standards is more crucial than ever, especially for government buyers. One key compliance standard is FIPS (Federal Information Processing Standards). Join us for an informative webinar where Kaleb Himes, Senior Software Engineer at wolfSSL, will guide you through the essential aspects of determining FIPS compliance.
Watch Today: How to Determine FIPS Compliance for Government Buyers
This webinar will cover:
- Why is FIPS important?
- Why is having a specific OE on the cert important?
- How to lookup a cert and determine if that cert fits your program requirements
- How to detect fake FIPS claims & Red Flags to lookout for
And more
This webinar is designed for government buyers who need to ensure that their systems meet the rigorous standards of FIPS. Kaleb will provide valuable insights and practical tips to help you navigate the complexities of FIPS compliance, avoid potential pitfalls, and make informed decisions.
Don’t miss this opportunity to enhance your understanding of FIPS compliance and safeguard your systems. Check it out for this exclusive webinar!
As always, our webinar includes Q&A throughout. If you have questions about any of the above, please contact us at facts@wolfSSL.com or +1 425 245 8247.
Download wolfSSL Now
wolfBoot Supports the Infineon AURIX TriCore TC3xx
We’re thrilled to announce that wolfBoot now supports Infineon’s AURIX TriCore TC3xx family of microcontrollers, bringing enhanced security and flexibility to your automotive and industrial applications.
Why AURIX TC3xx?
Infineon’s AURIX TriCore TC3xx microcontrollers are renowned for their high performance, safety, and security features, making them ideal for automotive and industrial applications. Adding wolfBoot to your TriCore application means you get a small and performant secure bootloader designed to protect your firmware right from the start.
Why wolfBoot on AURIX TC3xx?
- Security: Ensure only authenticated firmware runs on your TriCore device, safeguarding against malicious code and aftermarket tuning modifications. Encrypted application images prevent attackers from reverse engineering your code and data, and rollback protection ensures bugs in your firmware can’t be exploited once fixed. Secure key storage means your cryptographic material remains inaccessible from the outside world, providing your application with a strong root of trust.
- Reliability: Combine the TC3xx’s functional safety with wolfBoot’s robust image update procedure, providing your application with resilience to power failures and support for delta/incremental updates.
- Flexibility: wolfBoot is OS agnostic, and can interoperate with any RTOS, Linux or bare-metal application, including AUTOSAR stacks. wolfBoot’s tight integration with wolfCrypt, the world’s best-tested cryptography library, provides built-in support for all major cryptographic algorithms, including post-quantum algorithms and Chinese government-mandated SM ciphers. This means your application benefits from exceptional crypto agility, easily adapting to new cryptographic standards and staying secure against evolving threats.
Getting Started
To get started with wolfBoot on the AURIX TC3xx, clone the wolfBoot repository and follow the AURIX build instructions. The example project contains everything you need to load and update images on the AURIX LiteKit-V2 development board, but the steps should be adaptable to any device in the TC3xx family.
wolfBoot TriCore HSM Integration
wolfHSM is a software framework that provides a portable and open-source abstraction to hardware cryptography, non-volatile memory, and isolated secure processing that maximizes security and performance for ECUs. It consists of a client-server library architecture, where the wolfHSM server runs on the secure HSM core, and client applications communicate with the server through the wolfHSM client library. wolfHSM dramatically simplifies client applications by allowing direct use of wolfCrypt APIs, with the library automatically offloading all sensitive cryptographic operations to the HSM core as remote procedure calls with no additional logic required by the client app. The AURIX TC3xx family of devices is fully supported by wolfHSM, and includes HSM hardware crypto acceleration.
With the wolfHSM server running on the AURIX HSM core, wolfBoot can use the wolfHSM client to offload all cryptography and key storage to within the HSM secure environment, providing application images with an HSM-backed root of trust. wolfHSM can also leverage wolfBoot on the HSM core, authenticating both the wolfHSM server application and the TriCore application images before releasing wolfBoot on the application cores.
Using wolfBoot on the Infineon AURIX TC3xx is a big step towards securing your automotive or industrial application with minimal effort, especially when combined with wolfHSM.
If you have questions about any of the above, please contact us at facts@wolfSSL.com or +1 425 245 8247.
Download wolfSSL Now
wolfSSL Embraces RISC-V; FIPS 140-3 Certifications Now Available

wolfSSL was a proud sponsor and exhibitor at the RISC-V Summit EU earlier this year. Thank you to all the attendees that stopped by; We enjoyed the interesting discussions regarding wolfSSL in your projects.
Some of the most common questions we heard:
Q: Is wolfSSL supported on RISC-V devices?
A: Yes! Absolutely. The wolfSSL libraries run on nearly every device, including RISC-V. For instance, recently we published a blog on the HiFive Unleashed RISC-V Benchmarks.
Q: Does wolfSSL have support for RISC-V Acceleration Extensions?
A: Yes! For example, see the GitHub wolfSSL PR #7569 that implemented the AES ECB / CBC / CTR / GCM / CCM for RISC-V 64-bit in assembly language where we saw a 50x improvement in performance.
Q: Does wolfSSL have support for IP Hardware Acceleration such as OpenTitan?
A: We are currently evaluating Open Titan and various other IP solutions. We added RISC-V hardware acceleration to the Espressif ESP32-C3 and ESP32-C6 devices earlier this year.
Q: Can RISC-V devices be FIPS 140-3 Certified?
A: Yes! Recently we announced that wolfSSL is the First in the World to offer FIPS 140–3 Automated Submission with our NIST Certificate #4718.
See our prior blogs on:
- What is the difference between FIPS 140-2 and FIPS 140-3?
- FIPS vs FedRAMP Compliance and Requirements
The What is FIPS (short version) blog also applies to RISC-V with regards to how your RISC-V Operating Environment (“OE”) can be certified:
- You send us your hardware and toolchain.
- We run the initial tests which ensure the cryptography module behaves according to specification given your specific hardware and operating system.
- The CMVP certified lab runs and verifies the tests and their documentation.
- The test results are submitted to CMVP for review.
- Your specific operating environment is added to our certificate.
- You are FIPS 140 compliant in 60-90 days.
For more details, see our blog What is FIPS (long version).
Are you interested in RISC-V or FIPS Certification? We want to hear about your project!
If you have questions about any of the above, please contact us at facts@wolfSSL.com or +1 425 245 8247.
Download wolfSSL Now
FIPS 140-3 and KDF’s (Key Derivation Functions)
As our readers know, wolfSSL is currently the leader in embedded FIPS certificates. The wolfCrypt module holds the world’s first SP800-140Br1 FIPS 140-3 Validated Certificate #4718.
One of the things that is critical to our users is Key Derivation Functions.
Key derivation functions are consumed by TLS 1.2, TLS 1.3, and SSH. We will support KDF’s for all three in our new FIPS 140-3 certificate.
If you have questions on FIPS 140-3, please contact us at fips@wolfSSL.com or see our FIPS FAQ. For any other inquiries, please contact us at facts@wolfSSL.com or +1 425 245 8247.
Download wolfSSL Now
Why wolfSSH is Immune to the regreSSHion
Recently, Qualys found an exploit in OpenSSH’s sshd server application that they named regreSSHion. This exploit lets attackers run arbitrary code by exploiting a race condition in a signal handler.
wolfSSH is not a port or fork of OpenSSH. It is written from scratch by wolfSSL Inc. While wolfSSHd is using the same alarm signal to time out users, our signal handler only sets a flag. OpenSSH’s handler, on the other hand, called unsafe functions.
How wolfSSH Avoids This Vulnerability
wolfSSH’s signal handling is designed to be safer due to:
- Minimalist Signal Handling: Our handler only sets a flag, reducing race condition risks.
- Async-Signal Safe Operations: We ensure all operations within the signal handler are safe.
- Independent Implementation: wolfSSH is a complete rewrite, avoiding inherited vulnerabilities.
Conclusion
The regreSSHion exploit in OpenSSH underscores the need for safe signal handling. wolfSSH’s simple and secure approach to signal handling avoids the vulnerabilities found in OpenSSH, making it a safer choice for SSH server applications.
If you have any questions or want to talk about wolfSSH, please feel free to send us an email at facts@wolfssl.com or sales@wolfssl.com, or call us at +1 425 245 8247.
Download wolfSSL Now
Why Would You Want wolfSSL’s FIPS 140-3 Certificate
As our readers know, wolfSSL is currently the leader in embedded FIPS certificates. The wolfCrypt module holds the world’s first SP800-140Br1 FIPS 140-3 Validated Certificate #4718, valid through July 10th, 2029.
There are a few significant changes coming with FIPS 140-3. Over the years with many specification updates, a few things got a little inconsistent, so these inconsistencies have been brought back in line. wolfSSL is prepared to deliver the first and best implementation of FIPS 140-3, so get ready.
As FIPS 140-3 is the replacement for FIPS 140-2 it is always a good idea to switch over to it as soon as possible. You will also want wolfSSL’s FIPS 140-3 Certificate for many additional reasons that include:
- Merging the FIPS + ISO Standard
- CAST Testing Streamlined – just testing the algos they are actually using.
- Addition of TLS KDF in FIPS Boundary
- Addition of SSH KDF in FIPS Boundary
- Addition of RSA 4096
- Addition of ECDSA + SHA-3
- Removal of insecure algorithms: example Triple DES
Check out the wolfSSL embedded SSL/TLS library, star us on Github, and learn more about the latest TLS 1.3 is available in wolfSSL.
If you have questions about any of the above, please contact us at facts@wolfSSL.com or call us at +1 425 245 8247.
Download wolfSSL Now
Eclipse Mosquitto Broker with wolfSSL
The wolfSSL team has expanded our Open Source Projects repository with a port for Mosquitto, an open source MQTT broker. Mosquitto users can benefit from wolfSSL’s lightweight SSL/TLS library.
Why should you use wolfSSL with Mosquitto?
- Portability across platforms and OS/RTOS environments
- Low/optimized memory use (runtime and footprint)
- Best-tested SSL/TLS/crypto implementation available, reducing vulnerabilities
- Current protocol support, up to TLS 1.3
- Progressive algorithm support (ChaCha20, Poly1305, Curve/Ed25519, etc)
- Commercial support available direct from wolfSSL engineers
- Commercial licenses available (in addition to standard GPLv2)
To use the Mosquitto port, follow the instructions in the patch file.
Set up wolfSSL
git clone https://github.com/wolfSSL/wolfssl.git
cd wolfssl
./autogen.sh
./configure --enable-mosquitto
make
make install
Set up Eclipse Mosquitto
git clone https://github.com/eclipse/mosquitto.git
cd mosquitto
git checkout v2.0.18
patch -p1 <
make WITH_TLS=wolfssl
make WITH_TLS=wolfssl test
Let us know what you think! We plan to add support for CMake builds. If you are interested or have questions about any of the above, please contact us at facts@wolfssl.com or +1 425 245 8247.
Download wolfSSL Now
Weekly updates
Archives
- April 2025 (19)
- March 2025 (22)
- February 2025 (21)
- January 2025 (23)
- December 2024 (22)
- November 2024 (29)
- October 2024 (18)
- September 2024 (21)
- August 2024 (24)
- July 2024 (27)
- June 2024 (22)
- May 2024 (28)
- April 2024 (29)
- March 2024 (21)
- February 2024 (18)
- January 2024 (21)
- December 2023 (20)
- November 2023 (20)
- October 2023 (23)
- September 2023 (17)
- August 2023 (25)
- July 2023 (39)
- June 2023 (13)
- May 2023 (11)
- April 2023 (6)
- March 2023 (23)
- February 2023 (7)
- January 2023 (7)
- December 2022 (15)
- November 2022 (11)
- October 2022 (8)
- September 2022 (7)
- August 2022 (12)
- July 2022 (7)
- June 2022 (14)
- May 2022 (10)
- April 2022 (11)
- March 2022 (12)
- February 2022 (22)
- January 2022 (12)
- December 2021 (13)
- November 2021 (27)
- October 2021 (11)
- September 2021 (14)
- August 2021 (10)
- July 2021 (16)
- June 2021 (13)
- May 2021 (9)
- April 2021 (13)
- March 2021 (24)
- February 2021 (22)
- January 2021 (18)
- December 2020 (19)
- November 2020 (11)
- October 2020 (3)
- September 2020 (20)
- August 2020 (11)
- July 2020 (7)
- June 2020 (14)
- May 2020 (13)
- April 2020 (14)
- March 2020 (4)
- February 2020 (21)
- January 2020 (18)
- December 2019 (7)
- November 2019 (16)
- October 2019 (14)
- September 2019 (18)
- August 2019 (16)
- July 2019 (8)
- June 2019 (9)
- May 2019 (28)
- April 2019 (27)
- March 2019 (15)
- February 2019 (10)
- January 2019 (16)
- December 2018 (24)
- November 2018 (9)
- October 2018 (15)
- September 2018 (15)
- August 2018 (5)
- July 2018 (15)
- June 2018 (29)
- May 2018 (12)
- April 2018 (6)
- March 2018 (18)
- February 2018 (6)
- January 2018 (11)
- December 2017 (5)
- November 2017 (12)
- October 2017 (5)
- September 2017 (7)
- August 2017 (6)
- July 2017 (11)
- June 2017 (7)
- May 2017 (9)
- April 2017 (5)
- March 2017 (6)
- January 2017 (8)
- December 2016 (2)
- November 2016 (1)
- October 2016 (15)
- September 2016 (6)
- August 2016 (5)
- July 2016 (4)
- June 2016 (9)
- May 2016 (4)
- April 2016 (4)
- March 2016 (4)
- February 2016 (9)
- January 2016 (6)
- December 2015 (4)
- November 2015 (6)
- October 2015 (5)
- September 2015 (5)
- August 2015 (8)
- July 2015 (7)
- June 2015 (9)
- May 2015 (1)
- April 2015 (4)
- March 2015 (12)
- January 2015 (4)
- December 2014 (6)
- November 2014 (3)
- October 2014 (1)
- September 2014 (11)
- August 2014 (5)
- July 2014 (9)
- June 2014 (10)
- May 2014 (5)
- April 2014 (9)
- February 2014 (3)
- January 2014 (5)
- December 2013 (7)
- November 2013 (4)
- October 2013 (7)
- September 2013 (3)
- August 2013 (9)
- July 2013 (7)
- June 2013 (4)
- May 2013 (7)
- April 2013 (4)
- March 2013 (2)
- February 2013 (3)
- January 2013 (8)
- December 2012 (12)
- November 2012 (5)
- October 2012 (7)
- September 2012 (3)
- August 2012 (6)
- July 2012 (4)
- June 2012 (3)
- May 2012 (4)
- April 2012 (6)
- March 2012 (2)
- February 2012 (5)
- January 2012 (7)
- December 2011 (5)
- November 2011 (7)
- October 2011 (5)
- September 2011 (6)
- August 2011 (5)
- July 2011 (2)
- June 2011 (7)
- May 2011 (11)
- April 2011 (4)
- March 2011 (12)
- February 2011 (7)
- January 2011 (11)
- December 2010 (17)
- November 2010 (12)
- October 2010 (11)
- September 2010 (9)
- August 2010 (20)
- July 2010 (12)
- June 2010 (7)
- May 2010 (1)
- January 2010 (2)
- November 2009 (2)
- October 2009 (1)
- September 2009 (1)
- May 2009 (1)
- February 2009 (1)
- January 2009 (1)
- December 2008 (1)

