RECENT BLOG NEWS
wolfSSL on Microblaze
MicroBlaze, developed by Xilinx, is a soft processor core optimized for Xilinx FPGAs. It offers flexibility and scalability, making it suitable for a wide range of applications, including embedded systems and IoT devices. Integrating wolfSSL’s AES-GCM with MicroBlaze is possible and has been done running on a soft CPU on MicroBlaze. In the latest wolfSSL release this integration saw some additional enhancements. When used on a MicroBlaze, wolfSSL’s AES-GCM enhances the security capabilities of FPGA-based systems, enabling developers to implement secure communication protocols and data encryption mechanisms. There is also the option of setting up wolfSSL so that it makes use of Xilinx’s xilsecure while running on the Microblaze. Increasing the AES-GCM performance significantly.
For more information about using wolfSSL on a MicroBlaze or if you have questions about any of the above, please contact us at facts@wolfSSL.com or call us at +1 425 245 8247.
Download wolfSSL Now
RSA-PSS with CRL’s
Did you know wolfSSL has integration of RSA-PSS signatures with Certificate Revocation List (CRL) support?
RSA-PSS: Enhancing Security Layers
RSA-PSS, or Probabilistic Signature Scheme, represents a modern approach to digital signatures. Unlike traditional RSA signatures, RSA-PSS offers improved security properties, making it more resilient against various cryptographic attacks. By adopting RSA-PSS, wolfSSL users benefit from heightened security, enhancing the integrity of cryptographic operations.
Certificate Revocation List (CRL): Managing Certificate Integrity
In the realm of certificate management, CRL plays a pivotal role. It serves as a mechanism for indicating the revocation status of digital certificates. With CRL, systems can promptly identify and reject compromised or revoked certificates, bolstering the overall security posture. Integrating CRL support into wolfSSL empowers users with efficient certificate management capabilities, ensuring the authenticity and integrity of cryptographic transactions.
Empowering wolfSSL with RSA-PSS and CRL Integration
The fusion of RSA-PSS with CRL support within wolfSSL is a logical step when providing cutting-edge security solutions. Now, wolfSSL users can leverage the combined strength of RSA-PSS signatures and CRL management to fortify their cryptographic environments.
To delve deeper into the RSA-PSS with CRL integration in wolfSSL, visit our GitHub repository (https://github.com/wolfSSL/wolfssl/pull/7119) or reach out to facts@wolfSSL.com for assistance.
Thank you for entrusting wolfSSL as your ally in cybersecurity.
If you have questions about any of the above, please contact us at facts@wolfSSL.com or call us at +1 425 245 8247.
Download wolfSSL Now
Removal of user RSA
In the last release of wolfSSL there was some house cleaning done on older RSA implementations. The user RSA layer was removed along with the hooks used for tying in IPP. When those were first introduced we had yet to implement SP (single precision) versions of RSA. Fast forward to today, and there is a faster implementation of RSA in wolfSSL itself. In IPP v0.9 it was able to do 990.09 RSA 2048 bit sign operations per second and in wolfSSL 5.7.0 it was able to run 1,015.23 operations per second. Verify operations took around the same time with both libraries now at 35,714 operations per second on average. These measurements were collected on an older Intel(R) Core(TM) i7-4870HQ CPU. Along with a performant implementation of RSA there are now the crypto callbacks if desiring to plug in custom RSA operations. This being the case the –enable-fastrsa, user RSA, and IPP hooks were dropped to lower maintenance and reduce bundle size.
If you have questions about any of the above, please contact us at facts@wolfSSL.com or call us at +1 425 245 8247.
Download wolfSSL Now
Live Webinar: Migrating from Mocana to wolfSSL
Join our upcoming webinar, ‘Migrating from Mocana to wolfSSL,’ on May 2nd at 10 am PT hosted by wolfSSL Senior Software Engineer, Eric Blankenhorn. He will unveil the advantages of switching to wolfSSL, offering a superior alternative to Mocana with better support and a smoother workflow.
Watch the webinar here: Migrating from Mocana to wolfSSL
During this session, Eric will provide in-depth insights into what makes wolfSSL different from Mocana and address the gaps you might be experiencing while using Mocana. Discover a smooth transition from Mocana to wolfSSL, along with best practices for ensuring security continuity. Explore the potential benefits of using wolfSSL and learn how to optimize performance during the migration process. Let us introduce you to solutions that work best for your projects!
Watch now, for this informative webinar on migrating from Mocana to wolfSSL and ensure your cybersecurity remains robust and up-to-date!
As always, our webinars will include Q&A sessions throughout. If you have questions on any of the above, please contact us at facts@wolfSSL.com or call us at +1 425 245 8247.
Download wolfSSL Now
How to unload intermediate certificates with wolfSSL?
Recently, a notable modification was introduced in wolfSSL, a prominent provider of security solutions. Pull request #7245 (https://github.com/wolfSSL/wolfssl/pull/7245) focuses on optimizing memory management by introducing a function to unload intermediate CA certificates and free up memory. Let’s explore the significance of this code change and its potential impact on enhancing efficiency and resource utilization within cryptographic applications.
Specifically, the code change addresses the need to efficiently handle intermediate Certificate Authority (CA) certificates. These certificates, while essential for establishing trust chains in cryptographic operations, can consume valuable memory resources, particularly in resource-constrained environments.
The essence of the code change lies in the introduction of a dedicated function (wolfSSL_CertManagerUnloadIntermediateCerts()) to unload intermediate CA certificates from memory when they are no longer needed. By using this function, developers can optimize resource utilization, thereby enhancing the overall efficiency and stability of cryptographic operations.
Key Benefits: The introduction of the function to unload intermediate CA certificates brings several notable benefits:
- Efficient Memory Management: By providing a mechanism to unload intermediate CA certificates from memory, the code change ensures efficient utilization of resources. This is particularly crucial in environments where memory constraints are a concern, such as embedded systems and IoT devices.
- Prevention of Memory Leaks: Memory leaks can pose significant security and reliability risks in software applications. The new function helps prevent memory leaks by explicitly releasing memory allocated for intermediate CA certificates when they are no longer required, thereby improving the robustness of cryptographic operations.
- Scalability and Performance: Optimal memory management contributes to improved scalability and performance of cryptographic applications. By freeing up memory resources, the code change enables applications to handle larger workloads more efficiently, leading to enhanced responsiveness and overall performance.
By incorporating the function to unload intermediate CA certificates, developers can optimize resource utilization and mitigate potential security risks associated with memory management issues. This not only enhances the reliability and stability of cryptographic applications but also contributes to the overall security resilience of the systems in which they are deployed.
If you have questions about any of the above, please contact us at facts@wolfSSL.com or call us at +1 425 245 8247.
Download wolfSSL Now
ML-KEM and ML-DSA at the CAVP
The CAVP (Cryptographic Algorithm Validation Program) now has testing available for ML-KEM (Kyber) and ML-DSA (Dilithium). Initial Draft standards for these algorithms have been released as FIPS-203 and FIPS-204 respectively.
You can find the various .json test cases here:
- https://github.com/usnistgov/ACVP-Server/tree/master/gen-val/json-files/ML-DSA-keyGen-FIPS204
- https://github.com/usnistgov/ACVP-Server/tree/master/gen-val/json-files/ML-DSA-sigGen-FIPS204
- https://github.com/usnistgov/ACVP-Server/tree/master/gen-val/json-files/ML-DSA-sigVer-FIPS204
- https://github.com/usnistgov/ACVP-Server/tree/master/gen-val/json-files/ML-KEM-keyGen-FIPS203
- https://github.com/usnistgov/ACVP-Server/tree/master/gen-val/json-files/ML-KEM-encapDecap-FIPS203
Whenever you’re ready, we’ll be able to do CAVP testing of our implementations of these algorithms. Let us know about your interest in this!
If you have questions about any of the above, please contact us at facts@wolfSSL.com or call us at +1 425 245 8247.
Download wolfSSL Now
cURL Up 2024
Exciting news from cURL! We’re thrilled to announce the return of curl-up, scheduled to take place in Stockholm, Sweden from May 4th to the 5th! Our goal is to bring the community together for an unforgettable weekend of collaboration and learning.
We’re inviting all curl contributors, maintainers and fans to join us. Perfect opportunity for you to engage with Daniel Stenberg, the cURL founder, and maintainer of cURL, as well as other speakers and industry experts.
Save the date
- Date: May 4th to the 5th
- Location: Stockholm, Sweden
Stay updated on event details, including venue and agenda, on our dedicated web page, curl-up 2024. We’re open to agenda suggestions. Share your ideas on a curl mailing list or in the discussions section.
We would like to support our top-100 contributors with traveling and lodging expenses. Please read the funding attendance to see the regulation and eligibility requirements.
Registration is mandatory. Register now to secure your space! Let’s make curl-up 2024 an unforgettable weekend. See you there!
If you have questions about any of the above, please contact us at facts@wolfSSL.com or call us at +1 425 245 9247.
Download wolfSSL Now
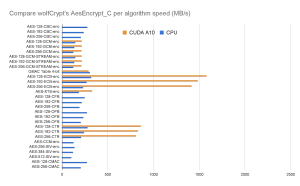
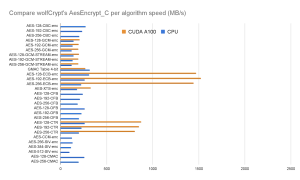
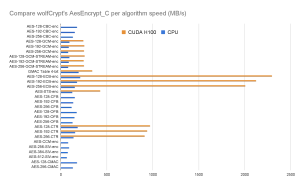
Accelerating AES Encryption with Nvidia CUDA: WolfCrypt Performance Boost
We have tested wolfCrypt using the Nvidia A10, A100, and H100 GPU architectures. Using the AesEncrypt_C function from wolfCrypt, we added the CUDA acceleration wrappers to determine the performance of the algorithm running on a GPU. The implementation simply hijacks the calls to AesEncrypt_C and AesEncryptBlock_C and uses the CUDA wrappers to run the function on the hardware. To gain performance, the hardware simultaneously calculates the blocks within the cipher instead of using a ‘for’ loop to iterate through.
The code is available for review as part of this merged PR. You now also have the option of comparing two benchmark results with our new ‘benchmark_compare.sh’ in the wolfSSL ‘scripts’ folder.
AES-GCM, AES-ECB, AES-XTS, and AES-CTR seem to get a 1.6x, 5x, 2.6x and 3x performance boost respectively on the A-series chips, and 2.6x, 10.8x, 3.5x and 5.3x boost on the H100, respectively. When the data to be encrypted is passed to the hardware, it calculates each block simultaneously as opposed to sequentially in the CPU.
Algorithms like AES-CBC, AES-CFB, AES-OFB, AES-CCM, AES-SIV and AES-CMAC grind to a halt because they can’t be independently parallelized. The output of the next block depends on the previous block.
Going forward, we are planning to optimize for even better cryptographic performance on GPUs. It just makes sense for us to add additional algorithmic support as well as full FIPS 140-3 support for Nvidia GPUs such that government consumers can have maximum assurance when encrypting sensitive video and audio with AES-XTS, for example.
If you need FIPS 140-3 encryption for GPUs it can be as simple as adding an operating environment to our certificate. See our contact details at the end of the post.
See some of the test results compared below:
Visit our download page to download the latest release, or clone it from wolfSSL GitHub. If you have questions about any of the above, feel free to email us at facts@wolfSSL.com or call us at +1 425 245 8247.
Share this blog on your favorite social platforms and let’s spark conversations that inspire positive change in AES encryption.
Download wolfSSL Now
wolfSSL Loves Robots!
Did you say robots? At wolfSSL we love robots! We even have one to clean our office in Bozeman, Montana. But even more than that little cleaner, we love securing robots.
If you are in the robotics and automation space, you already know that it’s all about scaling up. Sure a robot can clean an office, but that’s not the end goal. Once you’ve proven your product in one location, it can clean every location your client has. But in order to scale, you need a big customer. What better customer than government agencies?
But you need reliable security. That means confidentiality of all transmissions and proper authentication of all commands. That means authenticating your firmware to prevent tampering by nefarious actors. After all, you’re likely operating in healthcare, law enforcement or government. In all these industries, you’ll need to fulfill your regulatory requirements such as FIPS-140 or DO-178 before you even approach your customers. You specialize in making the robots do what they do so let our experts help you with those regulatory requirements.
Here at wolfSSL, we’ve helped numerous robotics companies with their FIPS-140 efforts with our support for the Robot Operating System (ROS).
But even more importantly than that, we support just about any real-time embedded platform you throw at us and have the best performance to boot! We understand you have millisecond real-time reaction requirements due to safety standards and can’t have processes locked up doing cryptographic operations. Send us a message asking about our asynchronous cryptographic APIs and we’ll set you up with a call with our expert engineers to hash out the details.
If you’re making robots, we need to have a conversation!
If you have questions about any of the above, please reach out to facts@wolfSSL.com or call us at +1 425 245 8247.
Download wolfSSL Now
Live Webinar: An introduction to Stateful Hash-Based Signature Schemes
Get ready to embark on a journey into another cutting-edge realm of cybersecurity with wolfSSL! Join us for an exciting webinar, “An Introduction to Stateful Hash-Based Signature Schemes,” led by Senior Software Developer Anthony Hu. Mark your calendars for April 25th at 10 am PT, as we explore the fundamentals of stateful hash-based signature schemes and their implications for the future of digital security.
Watch the Webinar Here: An Introduction to Stateful Hash-Based Signature Schemes
- Gain insight into the importance of staying ahead of the CNSA 2.0 timeline
- Dive into the One Time Signatures (OTS)
- Discover how Merkle Trees hierarchical data structures enhance security and scalability
-
Understanding the significance of the state in these algorithms
- Explore future advancements and beyond
And much more
Don’t miss out on this exclusive opportunity to boost your cybersecurity knowledge. This webinar promises to equip you with invaluable insights and practical skills to navigate the complexities of modern digital security.
Mark your calendar for April 25th at 10am PT and join us for an enlightening exploration of stateful hash-based signature schemes.
As always, our webinar includes Q&A sessions throughout. If you have any questions about any of the above, please contact us at facts@wolfSSL.com or call us at +1 425 245 8247.
Download wolfSSL Now
Weekly updates
Archives
- April 2025 (19)
- March 2025 (22)
- February 2025 (21)
- January 2025 (23)
- December 2024 (22)
- November 2024 (29)
- October 2024 (18)
- September 2024 (21)
- August 2024 (24)
- July 2024 (27)
- June 2024 (22)
- May 2024 (28)
- April 2024 (29)
- March 2024 (21)
- February 2024 (18)
- January 2024 (21)
- December 2023 (20)
- November 2023 (20)
- October 2023 (23)
- September 2023 (17)
- August 2023 (25)
- July 2023 (39)
- June 2023 (13)
- May 2023 (11)
- April 2023 (6)
- March 2023 (23)
- February 2023 (7)
- January 2023 (7)
- December 2022 (15)
- November 2022 (11)
- October 2022 (8)
- September 2022 (7)
- August 2022 (12)
- July 2022 (7)
- June 2022 (14)
- May 2022 (10)
- April 2022 (11)
- March 2022 (12)
- February 2022 (22)
- January 2022 (12)
- December 2021 (13)
- November 2021 (27)
- October 2021 (11)
- September 2021 (14)
- August 2021 (10)
- July 2021 (16)
- June 2021 (13)
- May 2021 (9)
- April 2021 (13)
- March 2021 (24)
- February 2021 (22)
- January 2021 (18)
- December 2020 (19)
- November 2020 (11)
- October 2020 (3)
- September 2020 (20)
- August 2020 (11)
- July 2020 (7)
- June 2020 (14)
- May 2020 (13)
- April 2020 (14)
- March 2020 (4)
- February 2020 (21)
- January 2020 (18)
- December 2019 (7)
- November 2019 (16)
- October 2019 (14)
- September 2019 (18)
- August 2019 (16)
- July 2019 (8)
- June 2019 (9)
- May 2019 (28)
- April 2019 (27)
- March 2019 (15)
- February 2019 (10)
- January 2019 (16)
- December 2018 (24)
- November 2018 (9)
- October 2018 (15)
- September 2018 (15)
- August 2018 (5)
- July 2018 (15)
- June 2018 (29)
- May 2018 (12)
- April 2018 (6)
- March 2018 (18)
- February 2018 (6)
- January 2018 (11)
- December 2017 (5)
- November 2017 (12)
- October 2017 (5)
- September 2017 (7)
- August 2017 (6)
- July 2017 (11)
- June 2017 (7)
- May 2017 (9)
- April 2017 (5)
- March 2017 (6)
- January 2017 (8)
- December 2016 (2)
- November 2016 (1)
- October 2016 (15)
- September 2016 (6)
- August 2016 (5)
- July 2016 (4)
- June 2016 (9)
- May 2016 (4)
- April 2016 (4)
- March 2016 (4)
- February 2016 (9)
- January 2016 (6)
- December 2015 (4)
- November 2015 (6)
- October 2015 (5)
- September 2015 (5)
- August 2015 (8)
- July 2015 (7)
- June 2015 (9)
- May 2015 (1)
- April 2015 (4)
- March 2015 (12)
- January 2015 (4)
- December 2014 (6)
- November 2014 (3)
- October 2014 (1)
- September 2014 (11)
- August 2014 (5)
- July 2014 (9)
- June 2014 (10)
- May 2014 (5)
- April 2014 (9)
- February 2014 (3)
- January 2014 (5)
- December 2013 (7)
- November 2013 (4)
- October 2013 (7)
- September 2013 (3)
- August 2013 (9)
- July 2013 (7)
- June 2013 (4)
- May 2013 (7)
- April 2013 (4)
- March 2013 (2)
- February 2013 (3)
- January 2013 (8)
- December 2012 (12)
- November 2012 (5)
- October 2012 (7)
- September 2012 (3)
- August 2012 (6)
- July 2012 (4)
- June 2012 (3)
- May 2012 (4)
- April 2012 (6)
- March 2012 (2)
- February 2012 (5)
- January 2012 (7)
- December 2011 (5)
- November 2011 (7)
- October 2011 (5)
- September 2011 (6)
- August 2011 (5)
- July 2011 (2)
- June 2011 (7)
- May 2011 (11)
- April 2011 (4)
- March 2011 (12)
- February 2011 (7)
- January 2011 (11)
- December 2010 (17)
- November 2010 (12)
- October 2010 (11)
- September 2010 (9)
- August 2010 (20)
- July 2010 (12)
- June 2010 (7)
- May 2010 (1)
- January 2010 (2)
- November 2009 (2)
- October 2009 (1)
- September 2009 (1)
- May 2009 (1)
- February 2009 (1)
- January 2009 (1)
- December 2008 (1)

