RECENT BLOG NEWS
wolfBoot v2.0.0 intel x86_64 support
wolfBoot v2.0.0 introduced support for the Intel x86-64 bit architecture by leveraging the Intel Firmware Support Package (Intel FSP) and several new exciting and interesting features: TPM integration, Multiboot2/ELF support, PCI support, AHCI support, SATA security features, and others.
On Intel x86_64, wolfBoot uses a dual stage design. In the first stage, It initializes the memory and the hardware with the help of Intel FSP. Intel FSP allows BIOS and bootloader developers to focus on the critical features and broad support without worrying about the hardware initialization details. After the memory and silicon initialization, wolfBoot enumerates and configures all PCI devices in the system.
In the second stage, when the hardware is up and ready, wolfBoot does the necessary steps to read, decrypt, verify, and safely boot the main application. We added support for AHCI controller, SATA disks and ATA security commands: the main application can now be stored in a password-locked hard drive!
In both stages, wolfBoot verifies each component loaded, either from system ROM or from the hard disk, plus the TPM support allows very interesting scenarios. First, it enables TPM-assisted measured boot: each component loaded into the system is “measured”, taking part in an integrity proof managed inside the TPM itself so that certain operations are allowed only if the system is in a trustful state. The TPM can store (“seal”) secrets that can be recovered (“unsealed”) only if the system is in a precise state. If compromised software is running on the target, the secret never leaves the TPM.
In wolfBoot we leverage this by sealing the disk password (randomly generated at the first boot) in the TPM and binding the unsealing to a precise state of the system. If the loaded components are compromised or if the disk is removed from the device for direct tampering, the disk can’t be unlocked at all!
Once the disk is unlocked, it’s time to load the application in the right place and communicate the current hardware situation before booting. wolfboot supports the Multiboot2 standards to communicate with the main application and it supports the Executable and Linkable Format (ELF) format, one of the most ubiquitous object file formats for binary distribution, to load the application in the right places into the memory. As it supports memory virtualization, the application can be loaded anywhere in the address space, even above the 4GB limit.
And, as always, all current features of wolfBoot such as verified boot, OTA firmware secure update with power-fail tolerance, delta updates, encrypted firmware, and post-quantum firmware verification, will be directly available on the Intel x86-64 architecture.
All these new features are supported on the VX3060 Kontron board and can be tested on QEMU, but new hardware will be supported soon. If you have a new Intel-based board you would like to have supported or for any other comments, feedback or questions, don’t hesitate to contact us at facts@wolfSSL.com or call us at +1 425 245 8247.
Download wolfSSL Now
Sniffing TLS Traffic
Do you have a need to capture and/or analyze TLS traffic? The wolfSSL library includes a useful tool that you can leverage. The wolfSSL sniffer can be used to capture TLS packets and even decrypt them when at least one of the keys is known. This can be done with both live and recorded PCAP traces.
This could be useful for several reasons, including:
- Analyzing Network Problems
- Detecting network misuse by internal and external users
- Monitoring network usage and data in motion
- Debugging client/server communications
The sniffer supports both TLS v1.2 and TLS v1.3. It can be integrated into any application using our sniffer API’s and it even comes with a complete working example!
See here for more detailed documentation.
Have any questions, comments, or suggestions? Contact us at facts@wolfSSL.com or call us at +1 425 245 8247.
Download wolfSSL Now
wolfSSL Rust Wrapper coming soon
Rust support is coming to wolfSSL this year! The wolfSSL embedded TLS library is a lightweight, portable, C-language-based SSL/TLS library known for its low footprint, speed, and feature set. Users have been able to take advantage of our library not only in C but also in their Java, C#, Python, and JavaScript projects using the various wrappers we provide. This year, we’re planning to add Rust to that list.
Similar to C, Rust is a low-level programming language with direct access to hardware and memory, which will make our wolfSSL Rust Wrapper a great SSL/TLS solution for embedded and IoT development for Rust projects. The wrapper will also service Rust users with performance and/or FIPS requirements.
Are you interested in a Rust wrapper?
If you have questions about any of the above, please contact us at facts@wolfSSL.com or call us at +1 425 245 8247.
Download wolfSSL Now
Live Webinar: Medical Device Security: Key Strategies for Cybersecurity and Data Protection
You are invited to join a webinar on “Medical Device Security: Key Strategies for Cybersecurity and Data Protection” scheduled for January 25th at 10 am PT. wolfSSL’s Senior Software Engineer, Eric, will delve into the topic of medical device security. As the complexity and connectivity of medical devices have increased, it is essential to maintain a high-quality security system to safeguard your data. Eric will showcase various use cases, demonstrate how wolfSSL products can enhance your security systems, explain the reasons why people choose wolfSSL for medical devices, and much more.
Watch the webinar here: Medical Device Security: Key Strategies for Cybersecurity and Data Protection
Don’t miss out on this opportunity to learn how you can protect your data from threats and provide peace of mind to your patients. Register today, and let us show you how you can leverage your security with wolfSSL!
As always, our webinars will include Q&A sessions throughout. If you have questions about any of the above, please contact us at facts@wolfSSL.com or call us at +1 425 245 8247.
Download wolfSSL Now
The Quantum Arena
It is always very interesting to see news articles about technical advances in the Quantum Arena. For example: https://www.scmp.com/news/china/science/article/3246752/china-and-russia-test-hack-proof-quantum-communication-link-brics-countries
This article talks about cooperation between China and Russia to make QKD (Quantum Key Distribution) between the two countries a reality. While only an experiment, this is a landmark achievement for the BRICS group of countries.
This is a great reminder that at a nation state level, most countries are diplomatically friendly while at the same time locked in fierce competition to gain technical superiority over each other. The Quantum Arena is one of those places where competition occurs. Of course, one of the other aspects of this arena is quantum computing. As the “Five Eyes” countries pour resources into developing quantum computers, so too do the BRICS countries. As competition heats up, it seems efforts are being redoubled to get to the first CRQC (Cryptographically Relevant Quantum Computer) on both sides.
Will you be ready upon the arrival of the first CRQC?
If you have questions about any of the above, please contact us at facts@wolfSSL.com or call us at +1 425 245 8247.
Download wolfSSL Now
X.509 Alternative Public Key and Signature
For people who work in the world of PKI (Public Key Infrastructure) and security protocols, when you think of certificates, RFC 5280 instantly comes to mind. However, it is interesting to note that this document was written in 2008 and is the IETF’s specification of X.509 which is itself a standard that is maintained by the ITU (International Telecommunication Union). The X.509 standard was updated in 2019.
One of the additions to X.509 made in 2019 is the concept of alternative cryptographic digital signature algorithm extensions. They are defined and discussed in technical detail in section 9.8 of the 2019 update to X.509.
Briefly, it introduces 3 new non-critical X.509 certificate extensions:
- Subject Alternative Public Key Information
- Alternative Signature Algorithm
- Alternative Signature Value
The main purpose of these extensions is to allow for 2 algorithms to be used in a certificate chain. The reason this is needed is to help ease the migration to post-quantum cryptography.
Do you think having an optional second alternative digital signature algorithm public key and signature in your certificates would be useful? If so, send a message to facts@wolfSSL.com and let us know your needs and use case for these X.509 extensions!
If you have questions about any of the above, please contact us at facts@wolfSSL.com or call us at +1 425 245 8247.
Download wolfSSL Now
wolfSSL Support for the Espressif ESP-IDF v5.2 Beta
Recently Espressif announced their ESP-IDF v5.2 Beta 1 on GitHub. The same day we found out about this exciting new version, we confirmed that all the wolfSSL Espressif ESP32 Examples are working in that environment. So far the “beta” looks to be well polished from our perspective. Last week, we learned about the ESP-IDF v5.2 Beta 2 on GitHub. The final release should be quite nice.
We have both core performance, benchmark, and client-server examples as well as additional examples for the ESP32.
Incorporating wolfSSL in your Espressif project has never been easier. As announced in the summer of 2023 – wolfSSL is now available in the Espressif ESP Registry of managed components: this one line adds wolfSSL to your project:
# Add wolfSSL component to existing ESP-IDF project idf.py add-dependency "wolfssl/wolfssl"
Get Started with wolfSSL
Additional information on getting Started with wolfSSL on the Espressif environment is available on the wolfSSL GitHub repository as well as this YouTube recording:
Find out more
If you have any feedback, questions, or require support, please don’t hesitate to reach out to us via facts@wolfSSL.com or call us at +1 425 245 8247, or open an issue on GitHub.
Download wolfSSL Now
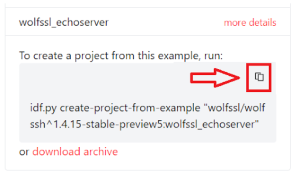
wolfSSH – Now Available as an Espressif Managed Component Includes SSH Echo Server Example

Not long ago, we announced preview support for new Espressif Managed Components. This is in addition to the core wolfssl managed component. Today you can add SSH capabilities to your toolbox by visiting this link:
https://components.espressif.com/components/wolfssl/wolfssh
If the ESP Registry page does not fully load with all the text, try holding down the “ctrl” key when pressing the refresh button in your browser. The CDN seems to occasionally cache incomplete web content.
Getting started with wolfSSL and wolfSSH has never been easier! You can add wolfSSH to your project with this command:
idf.py add-dependency “wolfssl/wolfssh”
We’ve also included a complete example project to connect to the AWS IoT MQTT. Just click the little “copy” icon and paste into a command prompt after the ESP-IDF has been installed:
Try it
Here’s an example of how the example can be created, built, and flashed onto your ESP32:
# Setup the ESP-IDF Environment (your actual path may vary)
. ~/esp/esp-idf/export.sh
# Download and create the example
idf.py create-project-from-example “wolfssl/wolfssh:wolfssh_echoserver”
cd wolfssl_echoserver
# Set your SSID and wifi Password in Example Connection Configuration
idf.py menuconfig
# Flash the code to your ESP32
idf.py -p /dev/ttyS9 -b 115200 flash monitor
The full wolfSSL repository for wolfSSH contains even more examples for not only this Echo Server Example, but many other target platforms as well.
Get Started with wolfSSL
Additional information on getting Started with wolfSSL on the Espressif environment is available on the wolfSSL GitHub repository as well as this YouTube recording:
Find out more
If you have any feedback, questions, or require support, please don’t hesitate to reach out to us via facts@wolfSSL.com, call us at +1 425 245 8247, or open an issue on GitHub.
Download wolfSSL Now
Live Webinar: Getting Started with wolfSSH in 2024
Join us for a webinar on ‘Getting Started with wolfSSH‘ scheduled for January 18th at 10 am PT. The latest release, wolfSSH v1.4.15, has just been unveiled as part of our Christmas releases! Packed with numerous features and improvements, this version promises an enriching experience.
wolfSSL Software Developer, Jacob Barthelmeh, will be your guide, starting from foundational knowledge and leading you to explore advanced features essential for initiating your journey with wolfSSH!
Watch the webinar here: Getting Started with wolfSSH
Sneak Peek of the webinar:
- SSH Overview
- Specifications supported by wolfSSH
- wolfSSH Architecture
- Configuration and Build Proces
- wolfSSH Examples and Applications
… and much more
Given that 2024 has just begun, this is an ideal moment to be part of our ‘Getting Started’ series! Don’t miss this chance to leverage the expertise of wolfSSL and harness wolfSSH’s potential for your projects! Bring all your wolfSSH-related questions; Jacob is ready to address them.
If you have questions about any of the above, please contact us at facts@wolfSSL.com or call us at +1 425 245 8247.
Download wolfSSL Now
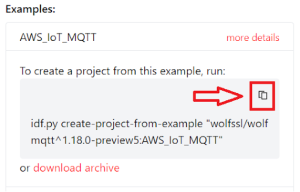
wolfMQTT – Now Available as an Espressif Managed Component Includes AWS IoT MQTT Example

Not long ago, we announced preview support for new Espressif Managed Components in addition to the core wolfssl managed component. Today you can add MQTT capabilities to your toolbox by visiting this link:
https://components.espressif.com/components/wolfssl/wolfmqtt
If the ESP Registry page does not fully load with all the text, try holding down the “ctrl” key when pressing the refresh button in your browser. The CDN seems to occasionally cache incomplete web content.
Getting started with wolfSSL and wolfMQTT has never been easier! You can add wolfMQTT to your project with this command:
idf.py add-dependency “wolfssl/wolfmqtt”
We’ve also included a complete example project to connect to the AWS IoT MQTT. Just click the little “copy” icon and paste into a command prompt after the ESP-IDF has been installed:
Try it
Here’s an example of how the example can be created, built, and flashed onto your ESP32:
# Setup the ESP-IDF Environment (your actual path may vary)
. ~/esp/esp-idf/export.sh
# Download and create the example
idf.py create-project-from-example “wolfssl/wolfmqtt:AWS_IoT_MQTT”
cd AWS_IoT_MQTT
# Set your SSID and wifi Password in Example Connection Configuration
idf.py menuconfig
# Flash the code to your ESP32
idf.py -p /dev/ttyS9 -b 115200 flash monitor
Tada! You have your very own sample MQTT AWS IoT device! Upon a successful connection, output similar to this should be displayed on the serial port being monitored:
I (17096) wolfmqtt main: Initial Stack Used (before wolfSSL Server): 2244 bytes
I (17104) wolfmqtt main: Starting awsiot_main...
AwsIoT Client: QoS 1, Use TLS 1
MQTT Net Init: Success (0)
MQTT Init: Success (0)
NetConnect: Host a2dujmi05ideo2-ats.iot.us-west-2.amazonaws.com, Port 8883, Timeout 5000 ms, Use TLS 1
MQTT TLS Setup (1)
MQTT TLS Verify Callback: PreVerify 0, Error -188 (ASN no signer error to confirm failure)
Subject's domain name is Starfield Services Root Certificate Authority - G2
Allowing cert anyways
MQTT Socket Connect: Success (0)
MQTT Connect: Proto (v3.1.1), Success (0)
MQTT Connect Ack: Return Code 0, Session Present 0
MQTT Subscribe: Success (0)
Topic $aws/things/demoDevice/shadow/update, Qos 1, Return Code 1
MQTT Publish: Topic $aws/things/demoDevice/shadow/update, ID 2, Success (0)
MQTT Waiting for message...
MQTT Message: Topic $aws/things/demoDevice/shadow/update, Qos 1, Len 92
Payload (0 - 92) printing 80 bytes:
{"state":{"reported":{"hardware":{"type":"wolf_aws_iot_demo","firmware_version":
MQTT Message: Done
The full wolfSSL repository for wolfMQTT contains even more examples for not only this Espressif AWS example, but many other target platforms as well.
Get Started with wolfSSL
Additional information on getting Started with wolfSSL on the Espressif environment is available on the wolfSSL GitHub repository as well as this YouTube recording:
If you have questions about any of the above, please contact us at facts@wolfSSL.com or call us at +1 425 245 8247.
Download wolfSSL Now
Weekly updates
Archives
- July 2025 (5)
- June 2025 (22)
- May 2025 (25)
- April 2025 (24)
- March 2025 (22)
- February 2025 (21)
- January 2025 (23)
- December 2024 (22)
- November 2024 (29)
- October 2024 (18)
- September 2024 (21)
- August 2024 (24)
- July 2024 (27)
- June 2024 (22)
- May 2024 (28)
- April 2024 (29)
- March 2024 (21)
- February 2024 (18)
- January 2024 (21)
- December 2023 (20)
- November 2023 (20)
- October 2023 (23)
- September 2023 (17)
- August 2023 (25)
- July 2023 (39)
- June 2023 (13)
- May 2023 (11)
- April 2023 (6)
- March 2023 (23)
- February 2023 (7)
- January 2023 (7)
- December 2022 (15)
- November 2022 (11)
- October 2022 (8)
- September 2022 (7)
- August 2022 (12)
- July 2022 (7)
- June 2022 (14)
- May 2022 (10)
- April 2022 (11)
- March 2022 (12)
- February 2022 (22)
- January 2022 (12)
- December 2021 (13)
- November 2021 (27)
- October 2021 (11)
- September 2021 (14)
- August 2021 (10)
- July 2021 (16)
- June 2021 (13)
- May 2021 (9)
- April 2021 (13)
- March 2021 (24)
- February 2021 (22)
- January 2021 (18)
- December 2020 (19)
- November 2020 (11)
- October 2020 (3)
- September 2020 (20)
- August 2020 (11)
- July 2020 (7)
- June 2020 (14)
- May 2020 (13)
- April 2020 (14)
- March 2020 (4)
- February 2020 (21)
- January 2020 (18)
- December 2019 (7)
- November 2019 (16)
- October 2019 (14)
- September 2019 (18)
- August 2019 (16)
- July 2019 (8)
- June 2019 (9)
- May 2019 (28)
- April 2019 (27)
- March 2019 (15)
- February 2019 (10)
- January 2019 (16)
- December 2018 (24)
- November 2018 (9)
- October 2018 (15)
- September 2018 (15)
- August 2018 (5)
- July 2018 (15)
- June 2018 (29)
- May 2018 (12)
- April 2018 (6)
- March 2018 (18)
- February 2018 (6)
- January 2018 (11)
- December 2017 (5)
- November 2017 (12)
- October 2017 (5)
- September 2017 (7)
- August 2017 (6)
- July 2017 (11)
- June 2017 (7)
- May 2017 (9)
- April 2017 (5)
- March 2017 (6)
- January 2017 (8)
- December 2016 (2)
- November 2016 (1)
- October 2016 (15)
- September 2016 (6)
- August 2016 (5)
- July 2016 (4)
- June 2016 (9)
- May 2016 (4)
- April 2016 (4)
- March 2016 (4)
- February 2016 (9)
- January 2016 (6)
- December 2015 (4)
- November 2015 (6)
- October 2015 (5)
- September 2015 (5)
- August 2015 (8)
- July 2015 (7)
- June 2015 (9)
- May 2015 (1)
- April 2015 (4)
- March 2015 (12)
- January 2015 (4)
- December 2014 (6)
- November 2014 (3)
- October 2014 (1)
- September 2014 (11)
- August 2014 (5)
- July 2014 (9)
- June 2014 (10)
- May 2014 (5)
- April 2014 (9)
- February 2014 (3)
- January 2014 (5)
- December 2013 (7)
- November 2013 (4)
- October 2013 (7)
- September 2013 (3)
- August 2013 (9)
- July 2013 (7)
- June 2013 (4)
- May 2013 (7)
- April 2013 (4)
- March 2013 (2)
- February 2013 (3)
- January 2013 (8)
- December 2012 (12)
- November 2012 (5)
- October 2012 (7)
- September 2012 (3)
- August 2012 (6)
- July 2012 (4)
- June 2012 (3)
- May 2012 (4)
- April 2012 (6)
- March 2012 (2)
- February 2012 (5)
- January 2012 (7)
- December 2011 (5)
- November 2011 (7)
- October 2011 (5)
- September 2011 (6)
- August 2011 (5)
- July 2011 (2)
- June 2011 (7)
- May 2011 (11)
- April 2011 (4)
- March 2011 (12)
- February 2011 (7)
- January 2011 (11)
- December 2010 (17)
- November 2010 (12)
- October 2010 (11)
- September 2010 (9)
- August 2010 (20)
- July 2010 (12)
- June 2010 (7)
- May 2010 (1)
- January 2010 (2)
- November 2009 (2)
- October 2009 (1)
- September 2009 (1)
- May 2009 (1)
- February 2009 (1)
- January 2009 (1)
- December 2008 (1)


