RECENT BLOG NEWS
OpenSSL 3.0 Provider solution with FIPS
As you may know, wolfSSL has integrated our FIPS-certified crypto module (wolfCrypt) with OpenSSL as an OpenSSL engine, a product we call wolfEngine. You may also know that OpenSSL 3.0 has done away with the engines paradigm in favor of a new concept, called providers. wolfSSL has begun work on an OpenSSL 3.0 provider, allowing you to use latest version of OpenSSL backed by our FIPS-certified wolfCrypt library. Like wolfEngine, the wolfSSL provider for OpenSSL is an excellent pathway for users looking to get FIPS compliance fast while still using OpenSSL.
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
wolfSSL adds Silicon Labs Hardware acceleration support
wolfSSL is excited to announce support for using Silicon Labs Hardware acceleration. The EFR32 family of devices support multiple wireless interfaces with hardware cryptographic operations. wolfSSL can now offload cryptographic operations for dramatically increased performance on the Silicon Labs EFR32 family!
Our new support includes hardware acceleration of the following algorithms:
- RNG
- AES-CBC
- AES-GCM
- AES-CCM
- SHA-1
- SHA-2
- ECDHE
- ECDSA
The new functionality can be enabled by defining WOLFSSL_SILABS_SE_ACCEL. In user_settings.h More details are available in the README.md in wolfcrypt/src/port/silabs of the wolfSSL tree.
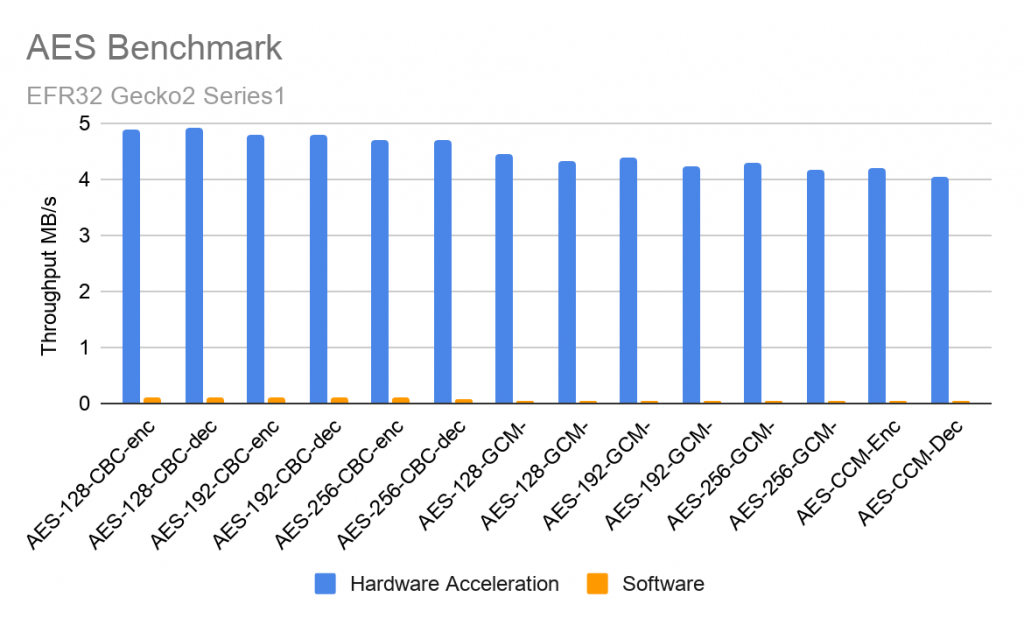
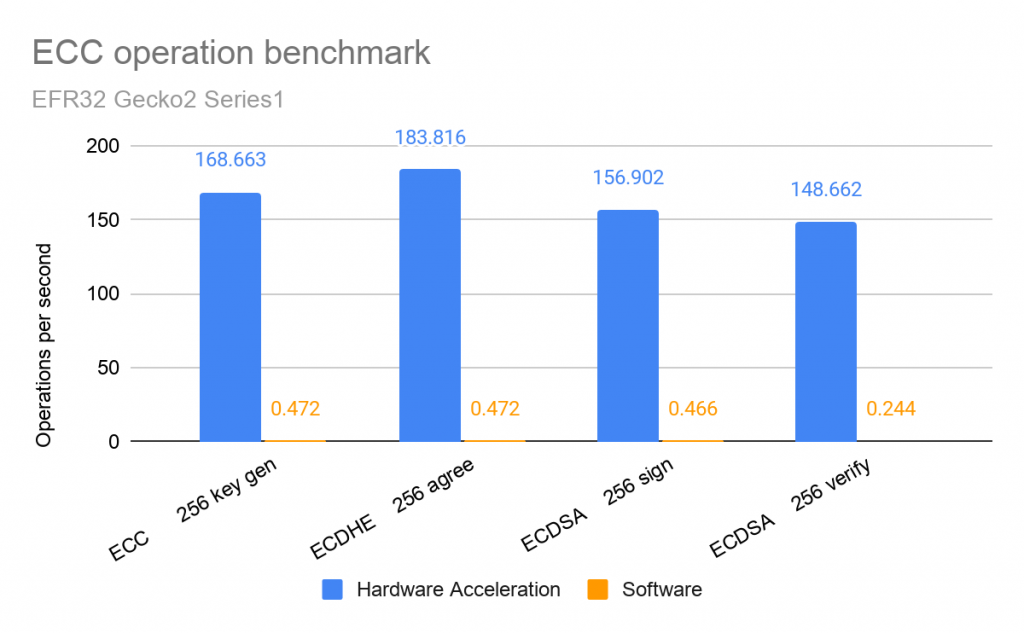
Benchmarks
Benchmark was performed on an EFR32 Gecko 2 (Series 1) using the xGM210P022.
The tests use Simplicity Studio v5 with Gecko SDK 3.0 using Micrium OS 5 and Secure Element Manager.
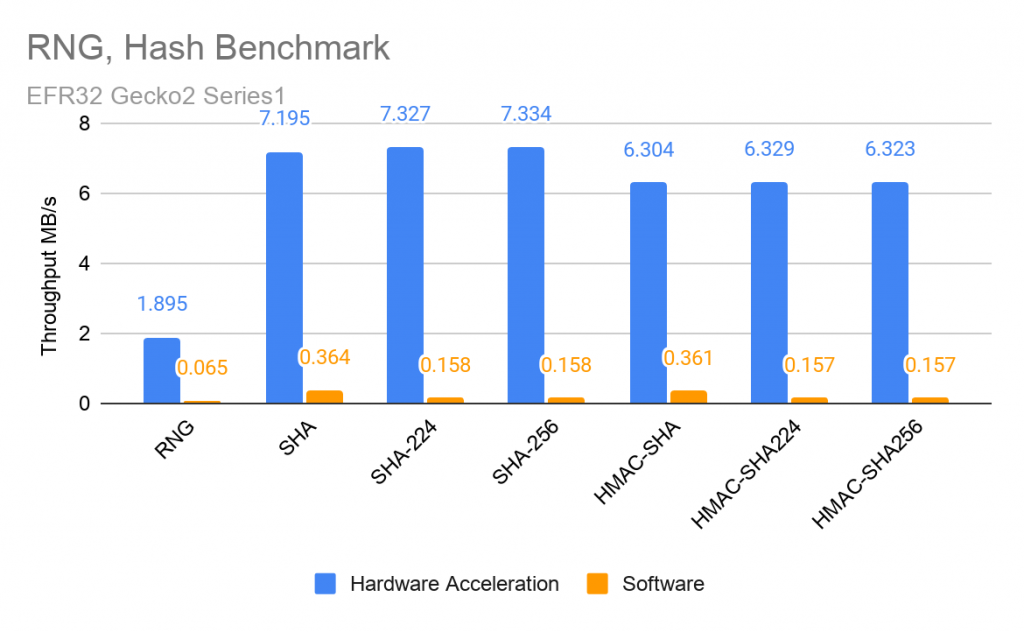
| Algorithm | Data Throughput (MB/s) |
| RNG | 1.895 |
| SHA | 7.195 |
| SHA-224 | 7.327 |
| SHA-256 | 7.334 |
| HMAC-SHA | 6.304 |
| HMAC-SHA224 | 6.329 |
| HMAC-SHA256 | 6.323 |
| AES-128-CBC-enc | 4.897 |
| AES-128-CBC-dec | 4.907 |
| AES-192-CBC-enc | 4.795 |
| AES-192-CBC-dec | 4.805 |
| AES-256-CBC-enc | 4.703 |
| AES-256-CBC-dec | 4.712 |
| AES-128-GCM-enc | 4.463 |
| AES-128-GCM-dec | 4.317 |
| AES-192-GCM-enc | 4.377 |
| AES-192-GCM-dec | 4.235 |
| AES-256-GCM-enc | 4.297 |
| AES-256-GCM-dec | 4.162 |
| AES-CCM-Enc | 4.203 |
| AES-CCM-Dec | 4.045 |
| ECC operation | Average time to complete (ms) | Operations per second |
| ECC 256 key gen | 5.929 | 168.663 |
| ECDHE 256 agree | 5.440 | 183.816 |
| ECDSA 256 sign | 6.373 | 156.902 |
| ECDSA 256 verify | 6.727 | 148.662 |
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
wolfSSL NXP SE050 Support Update
wolfSSL now supports NXP’s SE050 hardware security chip. This is an external I2C crypto co-processor chip that supports RSA key sizes up to 4096-bit, ECC curves up to 521 bit and ED25519 / Curve25519. You can see the full implementation details in GitHub pull request 4322.
We have also expanded our Kinetis LTC support to accelerate RSA key generation. This made it into our v4.8.1 release of wolfSSL.
NXP Semiconductor is a key member of wolfSSL’s partner network. wolfSSL ships with support for offloading cryptographic operations onto several NXP devices, such as the Coldfire, Kinetis, LPC, S32 and i.MX microprocessors. Additionally we support hardware cryptographic acceleration using NXP’s CAU, MMCAU, LTC, CAAM and SE050 hardware. If your target is missing, tell us!
wolfSSL develops a full suite of products supporting NXP designs. Learn about wolfBoot secure boot and TLS 1.3 firmware update with FreeRTOS and wolfSSL on NXP Freedom Board K64 here. After the release of wolfSSL version 4.2.0, we provide improved support for crypto hardware performance, now on NXP mmCAU. Download the latest wolfSSL version 4.8.1 here!
wolfSSL also provides surviving FIPS certificates that can be leveraged for your i.MX8, i.MX7 and i.MX8 CAAM projects. Stay tuned for upcoming FIPS 140-3 support.
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
Love it? Star us on GitHub!
Open Source Project Ports: tcpdump
wolfSSL is always adding new ports to our highly portable wolfCrypt library! We’re continuing our series on the latest open source project ports—this week, we’re featuring tcpdump.
We have integrated wolfSSL with tcpdump, a powerful command-line packet analyzer. This update allows for the use of tcpdump with our FIPS-validated crypto library, wolfCrypt. Tcpdump is a versatile tool with many options and filters, and is commonly used to capture or filter TCP/IP packets that are received or transferred over a network on a specific interface. Its long-running history ensures that there are many resources available for learning how to use this tool (See the tcpdump Wikipedia page for more info).
Through the OpenSSL compatibility layer, tcpdump is able to call into wolfSSL. Visit the GitHub page here: https://github.com/wolfSSL/osp/tree/master/tcpdump/4.9.3
Need more? Subscribe to our YouTube channel for access to wolfSSL webinars!
Love it? Star us on GitHub!
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
U-Boot with wolfTPM Update
News to look forward to—wolfSSL plans to integrate wolfTPM, our portable TPM 2.0 library, into U-Boot! This would extend the TPM 2.0 capabilities in U-Boot to include signature verification and measured boot.
For many platforms, we can replace U-Boot such as on the Xilinx UltraScale+ MPSoC.
wolfBoot is a portable secure bootloader solution that offers firmware authentication and firmware update mechanisms. Thanks to its minimalistic design, wolfBoot is completely independent from any OS or bare-metal application. Some of its key features include:
- Partition signature verification using ED25519, RSA and ECC
- Encryption of partitions
- Updating of partitions in the boot loader
- Measured boot with TPM 2.0 PCR registers
- Offloading to crypto coprocessors like the TPM 2.0 modules
- Version checking for updates
- Rollback on failed updates
For information on our wolfBoot TPM integration, visit https://www.wolfssl.com/curious-learn-wolfboot-tpm/.
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
RSA 3k or ECC 384 support in wolfBoot
Public key infrastructure or PKI is important term used to define everything that is used to “create, manage, distribute, use, store and revoke digital certificates and manage public-key encryption.” (https://en.wikipedia.org/wiki/Public_key_infrastructure) As RSA and ECC are one of the main algorithms used for PKI key generation, we are wondering if anyone is interested in RSA 3k or ECC 384 support in wolfBoot?
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
You can download the latest release here: https://www.wolfssl.com/download/
Or clone directly from our GitHub repository: https://github.com/wolfSSL/wolfBoot
While you’re there, show us some love and give the wolfBoot project a Star!
wolfSSL and libOQS Integration
wolfSSL has long been aware of the quantum threat to modern cryptography. Though quantum computing currently exists on small scales, research has determined enough to know that once full-scale quantum computing is available, all modern cryptography (RSA, ECC, etc.) will no longer be secure. Furthermore, the proven usage model of Quantum Computing as a Service (QCaaS) via the Cloud means that quantum capabilities will be more widely available, posing a greater security threat. This risk is why wolfSSL provides support for integration with the NTRU cryptosystem and an implementation of the QSH TLS extension.
With NIST already having announced the Round 3 finalists of the Post-Quantum Cryptography Competition, we thought it was time to update our quantum-safe offerings. WolfSSL will soon support integration with the Open Quantum-Safe project’s libOQS. Initial support will be for Key Exchange only using all parameter sets of Crystals-Kyber, NTRU, and SABER for TLS 1.3. With perfect forward secrecy, these algorithms can protect you from the “Harvest and Decrypt” threat model.
“Harvest and Decrypt”
If encrypted sensitive data is stolen (harvested) today, it will be accessible (decrypted) once a sufficiently-powered quantum computer is available. If the sensitive information has a secrecy requirement that extends beyond the time it will take to develop large-scale quantum computing, then that data should be considered at risk today. The quantum threat to current confidential data demonstrates the importance of migrating to quantum-safe solutions as soon as possible. For more details, you can look up “Mosca’s Inequality”.
Next Steps
To continue future-proofing encrypted data streams, wolfSSL plans to hybridize key construction algorithms with NIST-standardized ECDSA components. These hybridized algorithms will continue to be FIPS compliant under the current NIST standards. In addition, wolfSSL is developing a test for post-quantum cURL, coming in the next 4 to 6 weeks.
wolfSSL is attending ICMC (International Cryptographic Module Conference) this week, where we will be talking more about post-quantum computing—come visit us there!
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
Open Source Project Ports: libssh2
One of the highlights of our wolfCrypt library is its exceptional portability, which allows wolfSSL’s team of engineers to frequently add new ports! Stay tuned for the rest of our blog series on the latest open source project ports over the next few weeks.
This week, we’re showcasing libssh2! We have integrated wolfSSL with the libssh2 project, which allows for the use of libssh2 with our FIPS-validated crypto library, wolfCrypt. Libssh2 is a client-side C library designed to implement the SSH2 protocol for embedding specific SSH (Secure Shell) capabilities into other tools. The project includes hundreds of functions that allow specific activities and components to be selected and added to an application, while still remaining small in size.
We’ve enabled libssh2 to be able to call into wolfSSL through the OpenSSL compatibility layer. You can access the GitHub page here: https://github.com/wolfSSL/osp/tree/master/libssh2/1.9.0
Need more? Subscribe to our YouTube channel for access to wolfSSL webinars!
Love it? Star us on GitHub!
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
lighttpd Upstream Support
lighttpd has added support for wolfSSL in version 1.4.51! lighttpd is a fast and lightweight web server designed with a very low memory footprint. These design goals make wolfSSL an excellent choice as the SSL/TLS implementation, as it’s built to be lightweight, portable, and very fast. wolfSSL targets embedded and IoT devices but works just as well on desktop, enterprise, and cloud environments. Configuring wolfSSL as the SSL/TLS backend for lighttpd is simple and can provide you with the immediate benefit of a lower memory footprint and faster cryptography!
Compile wolfSSL with:
./configure --enable-lighty make make install
Compile lighttpd with:
./configure --with-wolfssl make make install
To learn about how to setup your lighttpd instance to use wolfSSL, please visit https://redmine.lighttpd.net/projects/lighttpd/wiki/Docs_SSL.
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
Love it? Star us on GitHub!
Open Source Project Ports: NTP
Because of the exceptional portability of our wolfCrypt library, plus our fantastic team of engineers, we’re able to frequently add new ports. We’ll be showcasing a few of the latest open source project ports over the next ten weeks, so tune in!
First, we just integrated wolfSSL with the NTP (Network Time Protocol) project. This port allows for the use of NTP with our FIPS-validated crypto library, wolfCrypt. NTP is designed to synchronize the clocks of computers over packet-switched, variable-latency data networks. For more information on NTP, you can also visit the project’s website at ntp.org.
We’ve enabled NTP to be able to call into wolfSSL through the OpenSSL compatibility layer. You can access the GitHub page here: https://github.com/wolfSSL/osp/tree/master/ntp/4.2.8p15
Need more? Subscribe to our YouTube channel for access to wolfSSL webinars!
Love it? Star us on GitHub!
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
Weekly updates
Archives
- May 2025 (9)
- April 2025 (24)
- March 2025 (22)
- February 2025 (21)
- January 2025 (23)
- December 2024 (22)
- November 2024 (29)
- October 2024 (18)
- September 2024 (21)
- August 2024 (24)
- July 2024 (27)
- June 2024 (22)
- May 2024 (28)
- April 2024 (29)
- March 2024 (21)
- February 2024 (18)
- January 2024 (21)
- December 2023 (20)
- November 2023 (20)
- October 2023 (23)
- September 2023 (17)
- August 2023 (25)
- July 2023 (39)
- June 2023 (13)
- May 2023 (11)
- April 2023 (6)
- March 2023 (23)
- February 2023 (7)
- January 2023 (7)
- December 2022 (15)
- November 2022 (11)
- October 2022 (8)
- September 2022 (7)
- August 2022 (12)
- July 2022 (7)
- June 2022 (14)
- May 2022 (10)
- April 2022 (11)
- March 2022 (12)
- February 2022 (22)
- January 2022 (12)
- December 2021 (13)
- November 2021 (27)
- October 2021 (11)
- September 2021 (14)
- August 2021 (10)
- July 2021 (16)
- June 2021 (13)
- May 2021 (9)
- April 2021 (13)
- March 2021 (24)
- February 2021 (22)
- January 2021 (18)
- December 2020 (19)
- November 2020 (11)
- October 2020 (3)
- September 2020 (20)
- August 2020 (11)
- July 2020 (7)
- June 2020 (14)
- May 2020 (13)
- April 2020 (14)
- March 2020 (4)
- February 2020 (21)
- January 2020 (18)
- December 2019 (7)
- November 2019 (16)
- October 2019 (14)
- September 2019 (18)
- August 2019 (16)
- July 2019 (8)
- June 2019 (9)
- May 2019 (28)
- April 2019 (27)
- March 2019 (15)
- February 2019 (10)
- January 2019 (16)
- December 2018 (24)
- November 2018 (9)
- October 2018 (15)
- September 2018 (15)
- August 2018 (5)
- July 2018 (15)
- June 2018 (29)
- May 2018 (12)
- April 2018 (6)
- March 2018 (18)
- February 2018 (6)
- January 2018 (11)
- December 2017 (5)
- November 2017 (12)
- October 2017 (5)
- September 2017 (7)
- August 2017 (6)
- July 2017 (11)
- June 2017 (7)
- May 2017 (9)
- April 2017 (5)
- March 2017 (6)
- January 2017 (8)
- December 2016 (2)
- November 2016 (1)
- October 2016 (15)
- September 2016 (6)
- August 2016 (5)
- July 2016 (4)
- June 2016 (9)
- May 2016 (4)
- April 2016 (4)
- March 2016 (4)
- February 2016 (9)
- January 2016 (6)
- December 2015 (4)
- November 2015 (6)
- October 2015 (5)
- September 2015 (5)
- August 2015 (8)
- July 2015 (7)
- June 2015 (9)
- May 2015 (1)
- April 2015 (4)
- March 2015 (12)
- January 2015 (4)
- December 2014 (6)
- November 2014 (3)
- October 2014 (1)
- September 2014 (11)
- August 2014 (5)
- July 2014 (9)
- June 2014 (10)
- May 2014 (5)
- April 2014 (9)
- February 2014 (3)
- January 2014 (5)
- December 2013 (7)
- November 2013 (4)
- October 2013 (7)
- September 2013 (3)
- August 2013 (9)
- July 2013 (7)
- June 2013 (4)
- May 2013 (7)
- April 2013 (4)
- March 2013 (2)
- February 2013 (3)
- January 2013 (8)
- December 2012 (12)
- November 2012 (5)
- October 2012 (7)
- September 2012 (3)
- August 2012 (6)
- July 2012 (4)
- June 2012 (3)
- May 2012 (4)
- April 2012 (6)
- March 2012 (2)
- February 2012 (5)
- January 2012 (7)
- December 2011 (5)
- November 2011 (7)
- October 2011 (5)
- September 2011 (6)
- August 2011 (5)
- July 2011 (2)
- June 2011 (7)
- May 2011 (11)
- April 2011 (4)
- March 2011 (12)
- February 2011 (7)
- January 2011 (11)
- December 2010 (17)
- November 2010 (12)
- October 2010 (11)
- September 2010 (9)
- August 2010 (20)
- July 2010 (12)
- June 2010 (7)
- May 2010 (1)
- January 2010 (2)
- November 2009 (2)
- October 2009 (1)
- September 2009 (1)
- May 2009 (1)
- February 2009 (1)
- January 2009 (1)
- December 2008 (1)

