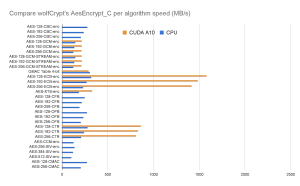
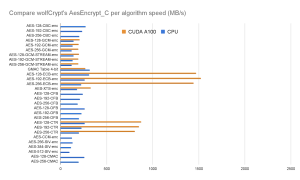
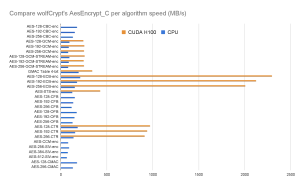
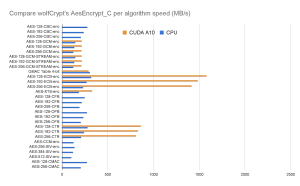
We have tested wolfCrypt using the Nvidia A10, A100, and H100 GPU architectures. Using the AesEncrypt_C function from wolfCrypt, we added the CUDA acceleration wrappers to determine the performance of the algorithm running on a GPU. The implementation simply hijacks the calls to AesEncrypt_C and AesEncryptBlock_C and uses the CUDA wrappers to run the function on the hardware. To gain performance, the hardware simultaneously calculates the blocks within the cipher instead of using a ‘for’ loop to iterate through.
The code is available for review as part of this merged PR. You now also have the option of comparing two benchmark results with our new ‘benchmark_compare.sh’ in the wolfSSL ‘scripts’ folder.
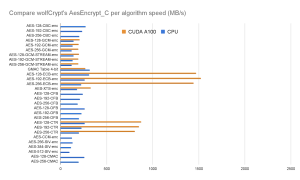
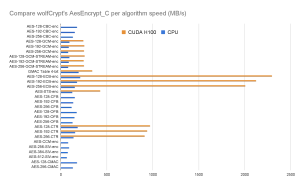
AES-GCM, AES-ECB, AES-XTS, and AES-CTR seem to get a 1.6x, 5x, 2.6x and 3x performance boost respectively on the A-series chips, and 2.6x, 10.8x, 3.5x and 5.3x boost on the H100, respectively. When the data to be encrypted is passed to the hardware, it calculates each block simultaneously as opposed to sequentially in the CPU.
Algorithms like AES-CBC, AES-CFB, AES-OFB, AES-CCM, AES-SIV and AES-CMAC grind to a halt because they can’t be independently parallelized. The output of the next block depends on the previous block.
Going forward, we are planning to optimize for even better cryptographic performance on GPUs. It just makes sense for us to add additional algorithmic support as well as full FIPS 140-3 support for Nvidia GPUs such that government consumers can have maximum assurance when encrypting sensitive video and audio with AES-XTS, for example.
If you need FIPS 140-3 encryption for GPUs it can be as simple as adding an operating environment to our certificate. See our contact details at the end of the post.
See some of the test results compared below:
Visit our download page to download the latest release, or clone it from wolfSSL GitHub. If you have questions about any of the above, feel free to email us at facts@wolfSSL.com or call us at +1 425 245 8247.
Share this blog on your favorite social platforms and let’s spark conversations that inspire positive change in AES encryption.
Download wolfSSL Now