We at wolfSSL continue to embrace the IoT market and congratulate all of the Espressif staff and partners on reaching the 1 Billion Device milestone in 2023. All of those devices need serious, commercial grade security with up to 7×24 support. We are here to help you do that! Of course, wolfSSL software cryptography works on any embedded device, but we’ve also added additional hardware acceleration support to Espressif SoC devices.
Recently our wolfSSL library has been upgraded to support the cryptographic hardware acceleration capabilities on Espressif ESP32 RISC-V SoC boards, specifically the ESP32-C2, ESP32-C3 and the ESP32-C6. The feature set is parity with our ESP32 and ESP32-S2/ESP32-S3 hardware acceleration capabilities which includes SHA (hash), RSA (big number math), and AES encryption. Additional new acceleration hardware capabilities specific to the newer Espressif chipsets are actively in development.
Although we are very proud of our software implementation, no programmatic algorithm can beat the brute strength of hardware acceleration. See below for some of the benchmark performance characteristics. The difference can be up to 10 times faster than equivalent software algorithms.
For instance: The ESP32-C6 has SHA acceleration implemented in hardware for SHA, SHA-224 and SHA-256, all of which are commonly used in TLS hashes. Here’s a comparison of the differences in performance for the ESP32C6:
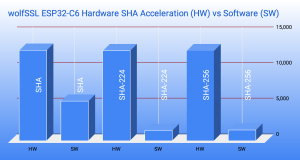
Taller bars represent more data hashed per second: KiB/s
Note the Espressif GitHub Issue #10423 for the latest ESP32-C6 support status. Silicon version 0.0 was used for testing and benchmarks noted above. Actual production values may differ.
See also our recent blogs:
- Secure Your Apple HomeKit Espressif ESP32 Devices with wolfSSL
- wolfSSL DTLS1.3 ESP32 Examples Now Available
- wolfSSL on the Espressif ESP32-C3 RISC-V
- wolfSSL on the Xtensa ESP32-S3 Linux
Additional information on getting Started with wolfSSL on the Espressif environment is available on the wolfSSL GitHub repository as well as a webinar recording, Getting Started with wolfSSL on the Espressif ESP32.
Try it yourself
If you’d like to see the benchmarks on your own device, ensure you have the ESP-IDF installed and follow these steps:
cd [your workspace directory] # Clone wolfSSL into a local directory git clone https://github.com/wolfSSL/wolfssl.git cd wolfssl/IDE/Espressif/ESP-IDF/examples/wolfssl_benchmark # Set your directory for ESP-IDF, shown here for VisualDGB and WSL WRK_IDF_PATH=/mnt/c/SysGCC/esp32/esp-idf/v5.1 # Run your ESP-IDF export.sh . ${WRK_IDF_PATH}/export.sh # or . $HOME/esp/esp-idf/export.sh # Set project target SoC idf.py set-target esp32c3 # optionally erase your device (substitute /dev/ttyS36 with your port) idf.py erase-flash -p /dev/ttyS36 -b 115200 # Build and flash the app onto your SoC (substitute /dev/ttyS36) idf.py build flash -p /dev/ttyS36 -b 115200 monitor -b 115200
Benchmark metrics for the ESP32-C6, Hardware Encryption Enabled:
Chip is ESP32-C6 (revision v0.0), Crystal is 40MHz, cpu freq: 160000000 Hz (160MHz)
------------------------------------------------------------------------------ wolfSSL version 5.6.4 ------------------------------------------------------------------------------ wolfCrypt Benchmark (block bytes 1024, min 1.0 sec each) RNG 1375 KiB took 1.005 seconds AES-128-CBC-enc 4450 KiB took 1.004 seconds AES-128-CBC-dec 4325 KiB took 1.004 seconds AES-192-CBC-enc 1450 KiB took 1.014 seconds AES-192-CBC-dec 1425 KiB took 1.010 seconds AES-256-CBC-enc 4425 KiB took 1.001 seconds AES-256-CBC-dec 4300 KiB took 1.001 seconds AES-128-GCM-enc 450 KiB took 1.044 seconds AES-128-GCM-dec 450 KiB took 1.044 seconds AES-192-GCM-enc 425 KiB took 1.002 seconds AES-192-GCM-dec 425 KiB took 1.002 seconds AES-256-GCM-enc 425 KiB took 1.004 seconds AES-256-GCM-dec 425 KiB took 1.005 seconds GMAC Default 602 KiB took 1.000 seconds 3DES 400 KiB took 1.051 seconds MD5 10775 KiB took 1.000 seconds SHA 12675 KiB took 1.000 seconds SHA-224 12625 KiB took 1.001 seconds SHA-256 12625 KiB took 1.001 seconds SHA-384 1275 KiB took 1.003 seconds SHA-512 1275 KiB took 1.003 seconds SHA-512/224 1275 KiB took 1.003 seconds SHA-512/256 1275 KiB took 1.003 seconds SHA3-224 925 KiB took 1.005 seconds SHA3-256 875 KiB took 1.008 seconds SHA3-384 675 KiB took 1.010 seconds SHA3-512 475 KiB took 1.019 seconds SHAKE128 1075 KiB took 1.009 seconds SHAKE256 875 KiB took 1.008 seconds RIPEMD 4325 KiB took 1.001 seconds HMAC-MD5 10650 KiB took 1.001 seconds HMAC-SHA 12475 KiB took 1.001 seconds HMAC-SHA224 12425 KiB took 1.001 seconds HMAC-SHA256 12425 KiB took 1.001 seconds HMAC-SHA384 1275 KiB took 1.019 seconds HMAC-SHA512 1275 KiB took 1.019 seconds PBKDF2 1 KiB took 1.005 seconds RSA 1024 key gen 1 ops took 1.262 sec, avg 1262.000 ms RSA 2048 key gen 1 ops took 1.680 sec, avg 1680.000 ms RSA 2048 public 6 ops took 1.415 sec, avg 235.833 ms RSA 2048 private 2 ops took 1.040 sec, avg 520.000 ms ECC [ SECP256R1] 256 key gen 4 ops took 1.290 sec, avg 322.500 ms ECDHE [ SECP256R1] 256 agree 4 ops took 1.280 sec, avg 320.000 ms ECDSA [ SECP256R1] 256 sign 4 ops took 1.296 sec, avg 324.000 ms ECDSA [ SECP256R1] 256 verify 2 ops took 1.240 sec, avg 620.000 ms CURVE 25519 key gen 4 ops took 1.276 sec, avg 319.000 ms CURVE 25519 agree 4 ops took 1.275 sec, avg 318.750 ms ED 25519 key gen 88 ops took 1.008 sec, avg 11.455 ms ED 25519 sign 78 ops took 1.022 sec, avg 13.103 ms ED 25519 verify 52 ops took 1.009 sec, avg 19.404 ms Benchmark complete
Benchmark metrics for the ESP32-C6, Hardware Encryption Disabled:
Chip is ESP32-C6 (revision v0.0), Crystal is 40MHz, cpu freq: 160000000 Hz (160MHz)
------------------------------------------------------------------------------ wolfSSL version 5.6.4 ------------------------------------------------------------------------------ wolfCrypt Benchmark (block bytes 1024, min 1.0 sec each) RNG 600 KiB took 1.023 seconds AES-128-CBC-enc 1725 KiB took 1.004 seconds AES-128-CBC-dec 1700 KiB took 1.010 seconds AES-192-CBC-enc 1500 KiB took 1.014 seconds AES-192-CBC-dec 1475 KiB took 1.013 seconds AES-256-CBC-enc 1325 KiB took 1.017 seconds AES-256-CBC-dec 1300 KiB took 1.012 seconds AES-128-GCM-enc 475 KiB took 1.041 seconds AES-128-GCM-dec 475 KiB took 1.042 seconds AES-192-GCM-enc 450 KiB took 1.030 seconds AES-192-GCM-dec 450 KiB took 1.030 seconds AES-256-GCM-enc 425 KiB took 1.012 seconds AES-256-GCM-dec 425 KiB took 1.012 seconds GMAC Default 621 KiB took 1.000 seconds 3DES 400 KiB took 1.051 seconds MD5 10750 KiB took 1.000 seconds SHA 5525 KiB took 1.002 seconds SHA-224 1450 KiB took 1.002 seconds SHA-256 1450 KiB took 1.001 seconds SHA-384 1275 KiB took 1.004 seconds SHA-512 1275 KiB took 1.003 seconds SHA-512/224 1275 KiB took 1.003 seconds SHA-512/256 1275 KiB took 1.003 seconds SHA3-224 925 KiB took 1.006 seconds SHA3-256 875 KiB took 1.008 seconds SHA3-384 675 KiB took 1.011 seconds SHA3-512 475 KiB took 1.019 seconds SHAKE128 1075 KiB took 1.009 seconds SHAKE256 875 KiB took 1.008 seconds RIPEMD 4325 KiB took 1.000 seconds HMAC-MD5 10650 KiB took 1.002 seconds HMAC-SHA 5475 KiB took 1.002 seconds HMAC-SHA224 1450 KiB took 1.010 seconds HMAC-SHA256 1450 KiB took 1.010 seconds HMAC-SHA384 1275 KiB took 1.019 seconds HMAC-SHA512 1275 KiB took 1.018 seconds PBKDF2 0 KiB took 1.075 seconds RSA 1024 key gen 1 ops took 7.733 sec, avg 7733.000 ms RSA 2048 key gen 1 ops took 28.050 sec, avg 28050.000 ms RSA 2048 public 58 ops took 1.028 sec, avg 17.724 ms RSA 2048 private 2 ops took 7.051 sec, avg 3525.500 ms ECC [ SECP256R1] 256 key gen 4 ops took 1.231 sec, avg 307.750 ms ECDHE [ SECP256R1] 256 agree 4 ops took 1.225 sec, avg 306.250 ms ECDSA [ SECP256R1] 256 sign 4 ops took 1.241 sec, avg 310.250 ms ECDSA [ SECP256R1] 256 verify 2 ops took 1.178 sec, avg 589.000 ms CURVE 25519 key gen 4 ops took 1.277 sec, avg 319.250 ms, 3.132 ops/sec CURVE 25519 agree 4 ops took 1.276 sec, avg 319.000 ms, 3.135 ops/sec ED 25519 key gen 87 ops took 1.001 sec, avg 11.506 ms, 86.913 ops/sec ED 25519 sign 78 ops took 1.018 sec, avg 13.051 ms, 76.621 ops/sec ED 25519 verify 52 ops took 1.023 sec, avg 19.673 ms, 50.831 ops/sec Benchmark complete
Find out more
If you have any feedback, questions, or require support, please don’t hesitate to reach out to us via facts@wolfSSL.com, call us at +1 425 245 8247, or open an issue on GitHub.
Download wolfSSL Now


